Doxxing is a type of cyberbullying that exposes your personal information, like your address or phone number. It’s malicious and can be extremely harmful to the targeted individual. Learn how doxxers find your information and how to prevent being doxxed.
What Is Doxxing?
Doxxing is searching for and publishing personal information about a person publicly with malicious intent. Doxxing includes the hacker analyzing information posted online about the victim in order to identify and then harass the victim. It can also involve exposing an anonymous account to reveal the person’s identity. The term “doxxing” comes from the expression “dropping dox” which refers to a method of revenge hacking that originated in the early 1990s. Hackers would “drop” malicious information on a rival using the internet.
Doxxing is usually meant to embarrass the victim, draw criticism towards them, get revenge or cause the victim physical harm. Doxxing is a very serious threat to your privacy and can ruin people’s lives. Larger doxxing attacks include public shaming and public humiliation on a large scale. Some people can lose their jobs, families or even their homes as a result of doxxing. Many are forced to change their identities and pay large sums of money to remove unwanted information online.
Where Does the Term Doxxing Come From?

Doxxing derives from the hacker word for “documents.” Documents shortened to “docs” and then “dox.” To “dox” someone means documenting their personal information. In the 1990s, hackers would “dox” an enemy or rival out of spite. This would involve hackers identifying the hacker and attempting to get the hacker arrested for illegal practices.
Nowadays, anyone can be doxxed because of the plethora of personal information that exists online. Hackers find out important information about you online such as your social security number, address, telephone number, social media accounts, name of relatives, etc.
What is the Purpose of Doxxing?
Doxxing is used as a weapon. The Anonymous group and similar movements use doxxing as a way to punish their enemies or people who disagree with what they stand for. They often do so by posting on message boards like 4chan, which has millions of members and hosts hate campaigns. 4chan has also included attacks in the form of fake telephone calls, an overload of abusive emails and a plethora of unwanted text messages.
Similar to identity theft, doxxing usually entails digging up information on the person through cyberstalking and hacking their credentials. While identity thieves’ main objective is financial gain, the goal of doxxing is more personal. Doxxing is typically for retribution, harassment or humiliation purposes.
How Does Doxxing Work?
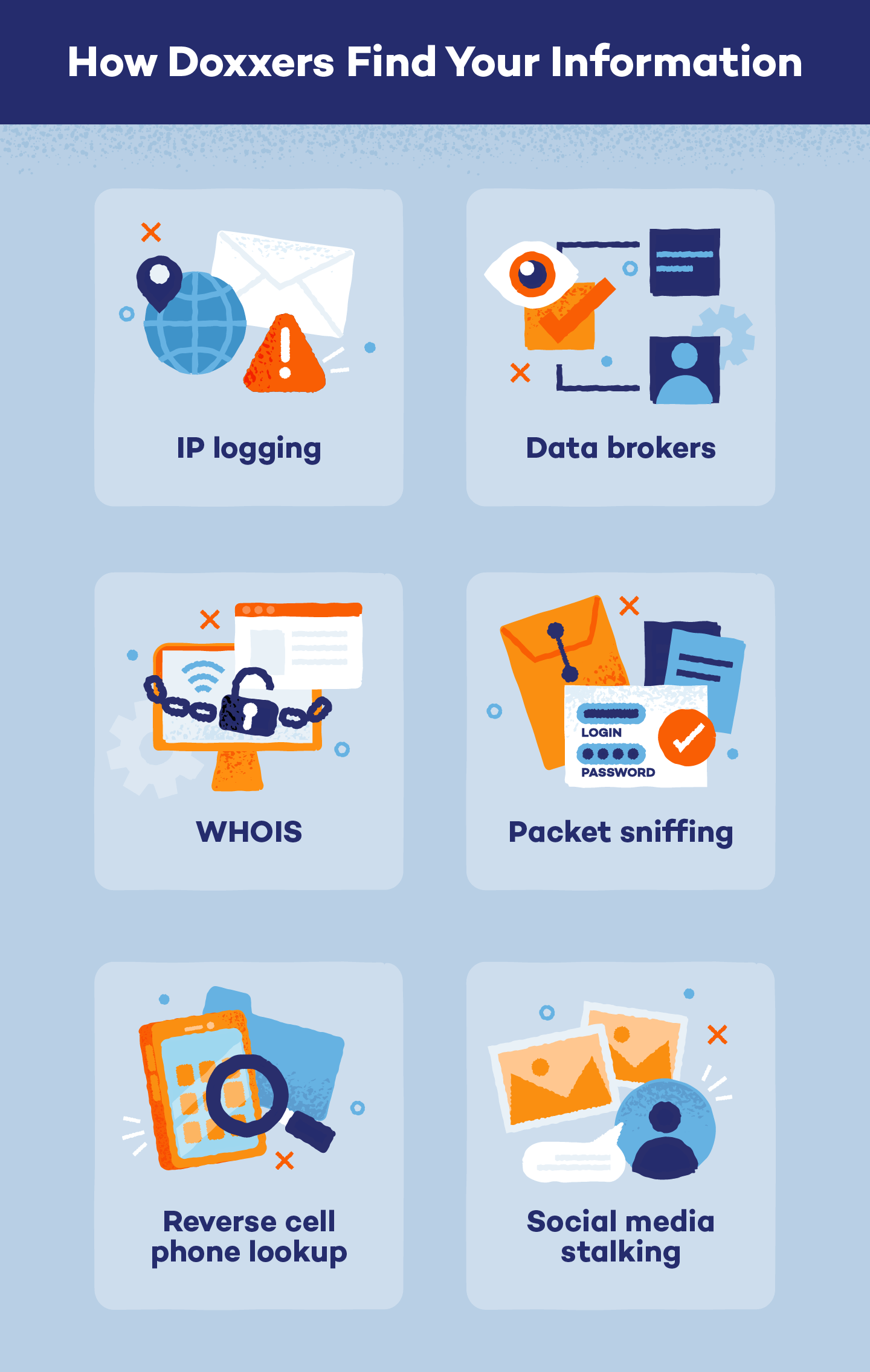
Now that you have learned what doxxing is, you may be wondering how doxxers find your information. There are a few techniques doxxers may use to retrieve information about you.
1
IP Logging
Every device has an IP address that details where the device is being used. Doxxers can use an IP logger (a piece of code you can’t see) to trace a victim’s online activities and determine where they’re located.
The IP logger is typically added to an email or a message to find out your IP address. Once a user has opened the message, the IP logger tracks you and exposes your identity by searching for accounts in your name on certain websites. It then sends your IP address back to the doxxer.
2
Data Brokers
Your information is dispersed throughout the web, especially if you have social media accounts or post public content. However, your information is also out there for people to find because of data brokers. Data brokers buy customer lists from other businesses, such as airlines, magazine subscription services and surveys or “enter to win” type sites. For example, you may have given one website your phone number, but now you receive dozens of calls a day from spammy or unknown callers.
The companies entice you to give your information for a reward and in their fine print or terms and conditions they state that they may sell your information. The data brokers then have the information readily available for doxxers and hackers to purchase. The good news is that some doxxers/hackers do not want to pay for the information, but to stay safe it’s important to remove yourself from data broker sites.
3
WHOIS
If you have created your own website, or use a website for your business, the registration information you used to receive the domain name becomes public to anyone using the WHOIS database. The data you have entered is accessible directly from the WHOIS website or through a domain sales broker. To ensure that you keep your data private, you can actually choose to obscure the information through your domain broker. You can also use an email that you use for subscriptions or an unimportant email address with a fake telephone number and fake information. It keeps you and your business safe and does not show up on the front end of your site.
4
Packet Sniffing
Data you send over a Wi-Fi network can be intercepted by a doxxer if they break into the Wi-Fi’s security measures. The doxxer can then access valuable information such as emails, passwords and bank account details.
5
Reverse Cell Phone Lookup
Doxxers use reverse cell phone lookup to find personal information about individuals. They enter a target’s phone number into online databases or specialised software to reveal details like the victim’s name, email, age and additional information by using their cell phone number.
6
Social Media Stalking
The majority of internet users have social media accounts. Doxxers will comb through public profiles, posts and comments for any fragments of data that they can piece together to form a comprehensive profile of a person.
This might include information such as names of relatives, birthdays, locations and more. Once they gain this initial information, they might resort to cross-referencing data from multiple sources, like exploiting gaps in privacy settings, using reverse image searches or engaging in phishing scams to obtain further sensitive data.
Real-Life Examples of Doxxing
Unfortunately, doxxing has become increasingly popular, and major incidents have occurred due to this toxic hacking technique. Below are a few well-known doxxing incidents:
Boston Marathon Bombing
Shortly after the Boston Marathon bombing in 2013, the Reddit community wrongly identified a few people as suspects. Even though the intent was to give law enforcement information on who to arrest, it ended up outing people who weren’t involved in the crime. This led to harsh consequences for the individuals who were wrongly accused, such as harassment on and offline.
Ashley Madison Data Breach
Ashley Madison is a well-known Canadian online dating service that’s targeted toward people in committed relationships. In 2015, a group known as The Impact Team stole Ashley Madison’s user data. They copied personal information about the site’s users and threatened to release the information if the site wasn’t immediately taken down. Because the site wasn’t shut down, the group leaked over 25 gigabytes of company data. This caused public humiliation and shaming, along with a few unconfirmed suicides due to stress and hate crimes.
Anonymous Exposes Thousands
In 2011, detailed information of over 6,000 law enforcement officials was exposed by Anonymous as a response to investigations into hacking activities. This incident brought doxxing into the public eye through media coverage, online message boards and social media platforms. In 2015, Anonymous struck again and released an official list of supposed members and supporters of the Ku Klux Klan.
How to Prevent Doxxing

The possibility of being doxxed is scary, but there are actions you can take to help prevent it from happening to you.
1
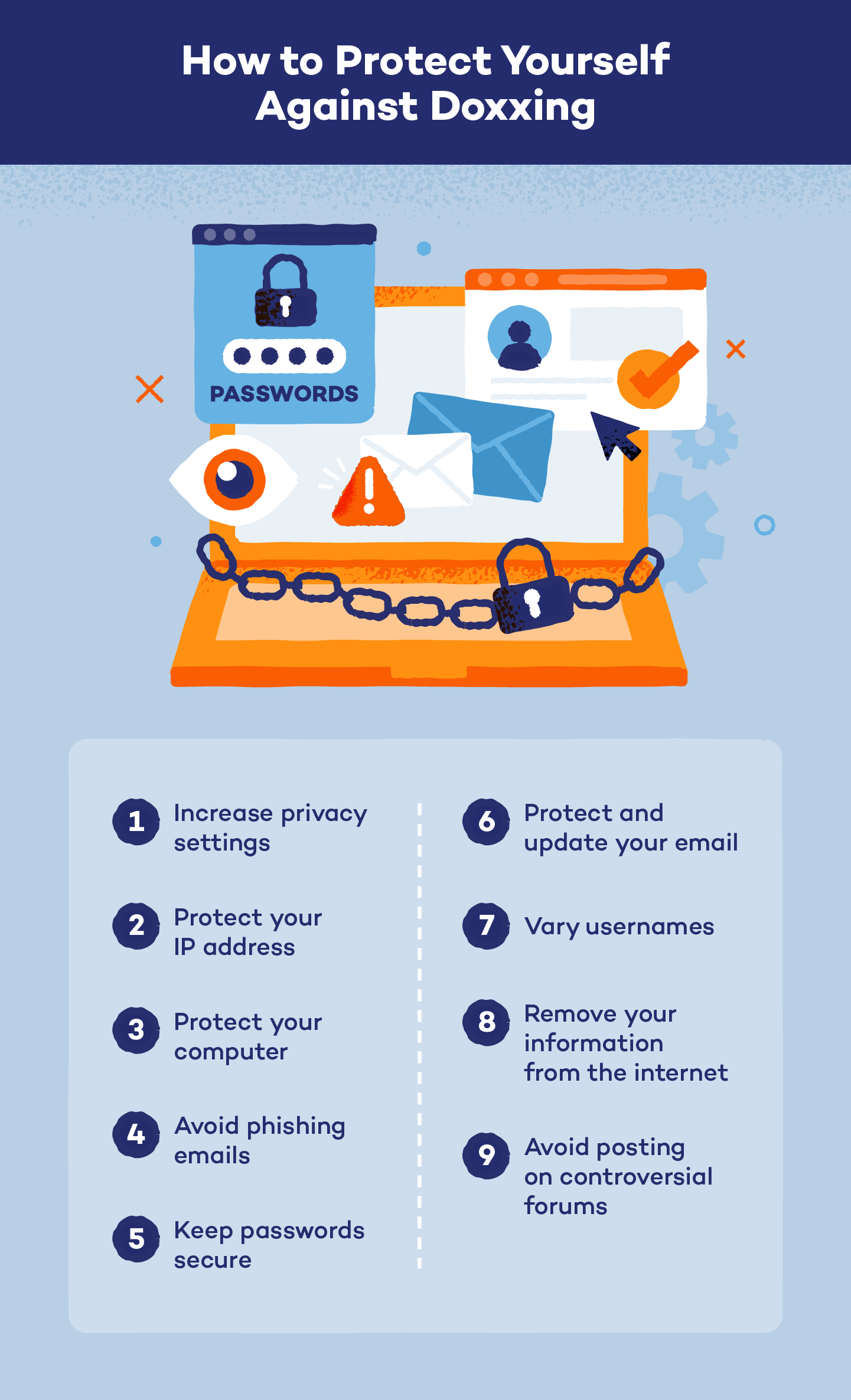
Increase Privacy Settings on Social Media
It’s important to keep personal information to a minimum on social media. Make sure you know each person you’re friends with on social media platforms. Only allow friends you know very well, and be wary of adding colleagues from work as competition could turn you into rivals.
Set your accounts to private and remove any addresses, places of work and specific locations from your accounts. Avoid discussing personal information that could be used against you. If you have children, never write where they go to school and avoid sharing images of them.
2
Protect Your IP Address
Every internet connection has an IP address that can be tracked back to your location. Installing a VPN eliminates this problem by keeping you anonymous online. Be wary of public Wi-Fi networks, as they could be fake hotspots put up by hackers to intercept your internet activity.
3
Protect Your Computer
Doxware is malware or spyware, which can steal your personal information and passwords for online services. Because doxware is malware, it’s important to keep your computer up-to-date and secure. Install an antivirus and check for updates frequently to keep doxware from intercepting your device.
4
Avoid Phishing Emails
Phishing emails disguise themselves as legitimate messages to trick you into revealing sensitive information. Exercise caution when opening emails from unfamiliar senders. Never click on suspicious links or download emails unless they’re from a legitimate sender. Falling for a phishing email can give hackers access to your computer to download malware that can collect your personal information.
5
Keep Passwords Secure
Doxxers will try to find anything they can to use against you and intercept your accounts. Prevent doxxing by creating strong passwords. They should be at least 14 characters, a variety of letters, numbers and special characters, and have no tie to personal information, like a birthdate or Social Security number. Use a password manager like LastPass or 1Password to create secure, strong passwords for each account.
6
Protect and Update Your Email
Create a separate, “fun” email for all of those sites that require an email address for registration. This includes any kind of subscription service or email blast that you want to be a part of, but don’t in your primary inbox. It’s a good idea to give away this email when you feel the site or service may not be very secure. Some of these websites may be doxxing harvesting sites, and if you use an unimportant email you are able to delete your account and information without a scratch. Be sure to make the email address unrelated to your name or your hobbies.
7
Vary Usernames
Create unique usernames for each individual website you hold an account with. If you are signed up for a controversial website or forum, make sure your username is anonymous and cannot be traced back to you. For social media, avoid using your first and last name in your handles.
8
Remove Your Information From the Internet (Self-Doxxing)
In order to find out if you’re susceptible to doxxing, it’s important to know what information about you is online. The process of protecting yourself from information leakage is known as “self-doxxing.” This involves researching information about you that is publicly available on the web.
Check out We Leak Info to find out where hackers can find you online. You can also check out the following list of data brokers and ask them to remove your data. Some require payment, and some require you to mail in information. However, once you’ve exhausted this list, you can feel more confident that your personal and private information is secure.
9
Avoid Posting on Controversial Forums
Because we have so much freedom online, it’s crucial that you’re thoughtful with everything we share online. While it might seem like a good idea to voice your opinion on a public forum, try to avoid it. Posting controversial views on any internet database can be threatening to you and to your friends and family. If you still intend to share your strong views, be sure to take extra precautions to stay anonymous online. Use pseudonyms when posting comments online and never share your location or full name.
Doxxing FAQ
Have more questions about doxxing? Check out these answers to common questions.
Is Doxxing Illegal?
Doxxing is only illegal if it applies to the following groups:
- Any officer or employee of the United States
- Jurors or witnesses of a court case
- Informants or witnesses of a federal criminal investigation
- State or local officer or employee whose restricted personal information is made public because of the participation in a federal criminal investigation
Can You Go to Jail for Doxxing?
You can’t go to jail only for doxxing. However, doxxing can be connected to the following crimes, which you can go to jail for:
- Harassment
- Stalking
- Identity theft
- Inciting violence
- Invasion of privacy
What Is Swatting?
Swatting is when the police or SWAT units are “prank-called” to someone’s home. If a person is getting doxxed online, it can lead to swatting. Malicious hackers will find the victim’s address and make false bomb threats or other serious situations that cause the police to show up to the unaware victim’s home. Swatting is becoming increasingly common as a form of revenge and can cause serious consequences.
Doxxing can be extremely detrimental, but it’s also preventable. Learn more about how to protect your personal information online so you can avoid cyber threats like doxxing.






