Glossary
Easy-to-understand definitions for common cybersecurity terms and topics.
Hello!
You’re about to visit our web page in English
Would you like to continue?
If this is not what you’re looking for,
A rootkit is a set of tools or malicious software designed to hide the presence of other programs or processes on a computer system, thereby making it difficult for users or even antivirus solutions to detect them. Although not always dangerous in their own right, they can be used by cybercriminals to hide malware and remotely access systems without being detected.
Rootkits can affect operating systems, firmware, or even hardware, and give adversaries persistent control over a compromised device.
The main purpose of a rootkit is to hide the presence of threats or tools used by attackers, in order to:
A rootkit manipulates components deep inside an operating system, such as the kernel or the process table, hiding its own traces and those of any other associated threats. It can be integrated into the system boot process or load modules dynamically, allowing it to go undetected even with traditional security tools.
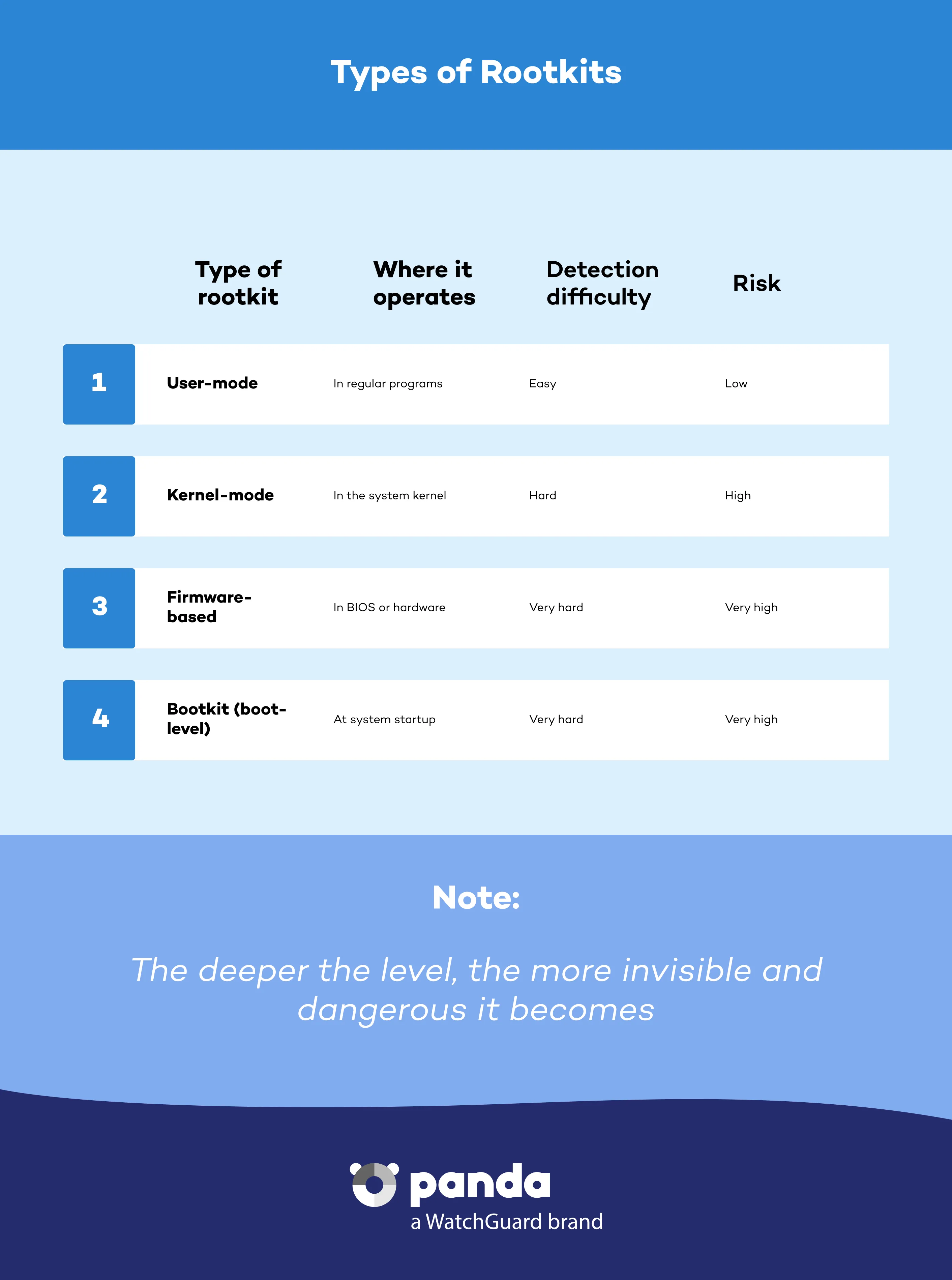
There are several types of rootkits, classified according to the system level at which they operate:
These run as normal applications and are easier to detect. They can hide files, processes, and registry keys, but they do not have complete control over the system.
These operate in the operating system kernel, which enables them to intercept and manipulate system calls. They are very difficult to detect and remove.
These are installed in the firmware of devices such as motherboards or BIOS/UEFI. They persist even after formatting the hard drive or reinstalling the operating system.
These modify the system boot process in order to load malware before loading the operating system, thereby ensuring that it runs before any security software can be activated.
Detecting a rootkit is complex due to their ability to conceal themselves. Warning signs include:
To identify and remove a rootkit, it is advisable to use advanced offline scanning solutions or specialized tools. Panda Dome can help with this process.
Removing a rootkit may require several steps:
In some cases, the safest option is to completely reinstall the operating system or update the firmware from official sources.
Prevention is the best protection against rootkits:

Panda Dome provides multi-layered defense that includes:
You can also reinforce your cybersecurity with different solutions from Panda Security:
Also, help from our support center to respond to any incident.
Although both are tools used by attackers, a Trojan disguises itself as legitimate software to enter the system, while a rootkit hides its presence and that of other malware.
Yes. Many rootkits hide spyware or keyloggers that record confidential information such as passwords, email addresses, or banking details
Yes. A rootkit is designed to avoid detection, so you could be infected without noticing any symptoms. The best defense is a solution such as Panda Dome with advanced scanning.
Discover the Panda Dome plan that best fits your needs
You can take a look to every single product page (Panda Dome Essential, Panda Dome Advanced, Panda Dome Complete and Panda Dome Premium) or compare all our plans to take a decision.
Digital security is everyone's responsibility. With the right information and tools, you can reduce risks and use the Internet with peace of mind. Explore our guides and protect your online privacy.
Glossary
Easy-to-understand definitions for common cybersecurity terms and topics.
Panda Security Blog
Discover expert advice, detailed tips, and the latest cybersecurity news.

Panda Security, a WatchGuard Technologies brand, offers the most advanced protection for your family and business. Its Panda Dome range provides maximum security against viruses, ransomware and computer espionage, and is compatible with Windows, Mac, Android and iOS.








