Glossary
Easy-to-understand definitions for common cybersecurity terms and topics.
Hello!
You’re about to visit our web page in English
Would you like to continue?
If this is not what you’re looking for,
Rogueware is a type of malicious software that masquerades as legitimate security software —such as an antivirus— to trick users into believing their computer is infected. The aim is to scare users with fake virus alerts or warnings of security issues to trick them into paying for a fraudulent solution that doesn't actually eliminate any real threats.
This malware often displays interfaces very similar to those of legitimate products, and can even show fake scan reports to appear credible.
Rogueware uses scareware techniques to psychologically manipulate users. Common features include:
The main objective is to extort money from unsuspecting users, though it can also be used to install other types of malware on a system.
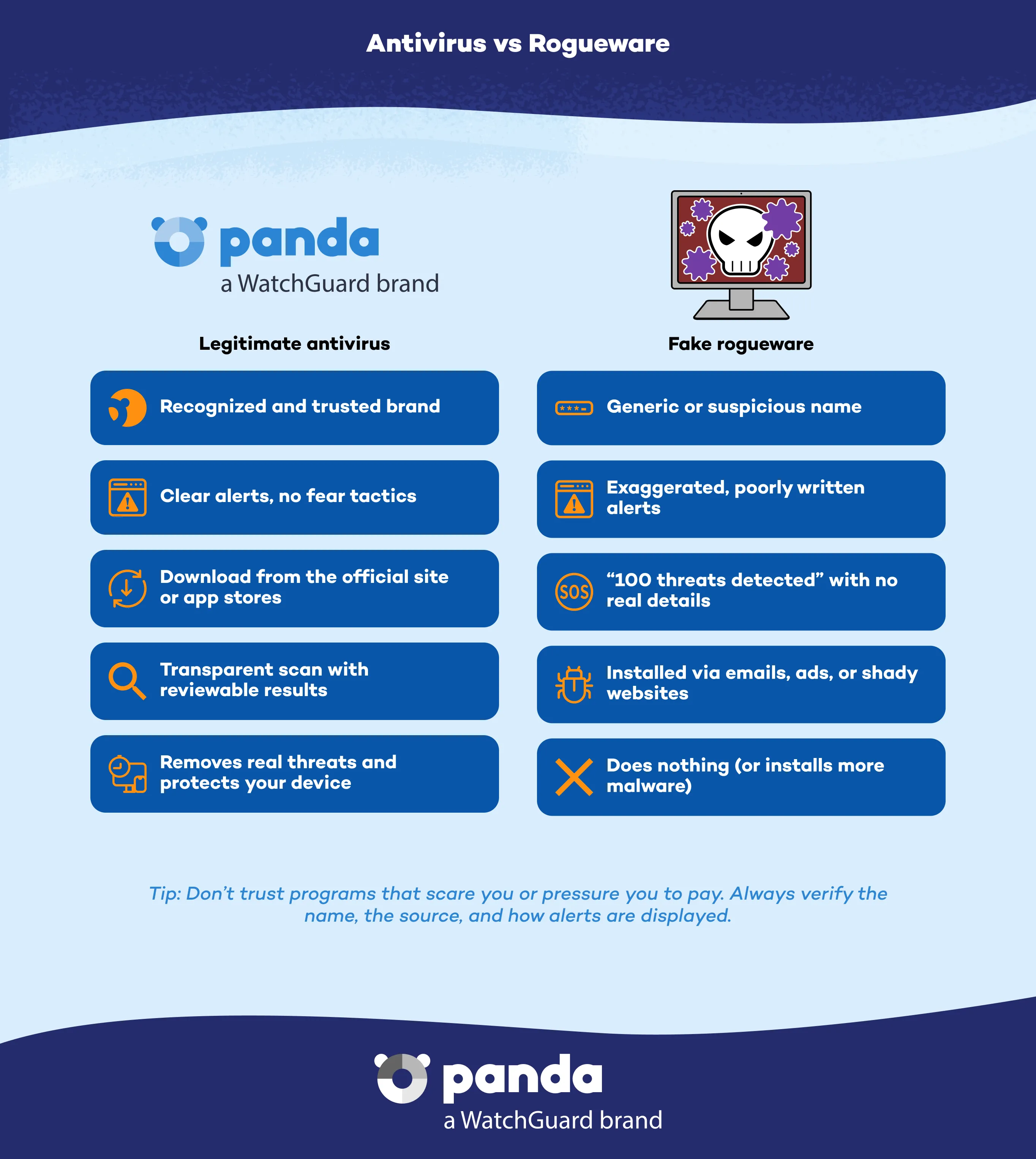
While rogueware is a variant of scareware, the main difference is that rogueware claims to be legitimate security software, while scareware may simply display fake alerts without pretending to be an antivirus.

There are many versions of rogueware on the market, tailored to different audiences and geographical regions. Some notable examples that have been detected and analyzed include:
Preventing rogueware infection requires caution and the use of reliable security tools. Here are some tips:
Panda Dome provides advanced protection that detects and blocks rogueware thanks to:
With Panda Dome, you can avoid being scammed and keep your devices free from threats.
Disconnect your computer from the Internet, don't pay any ransoms or purchase unknown programs, and use a reliable antivirus to clean your system.
Because it aims to trick users with false alerts in order to obtain money and can also leave devices vulnerable to further attacks.
Yes, some variants are designed to mimic legitimate antivirus solutions or even operating system programs, making them difficult to detect.
Rogueware is spread through fraudulent emails, compromised websites, SMS messages, or malicious advertising.
Discover the Panda Dome plan that best fits your needs
You can take a look to every single product page (Panda Dome Essential, Panda Dome Advanced, Panda Dome Complete and Panda Dome Premium) or compare all our plans to take a decision.
Digital security is everyone's responsibility. With the right information and tools, you can reduce risks and use the Internet with peace of mind. Explore our guides and protect your online privacy.
Glossary
Easy-to-understand definitions for common cybersecurity terms and topics.
Panda Security Blog
Discover expert advice, detailed tips, and the latest cybersecurity news.

Panda Security, a WatchGuard Technologies brand, offers the most advanced protection for your family and business. Its Panda Dome range provides maximum security against viruses, ransomware and computer espionage, and is compatible with Windows, Mac, Android and iOS.








