Glossary
Easy-to-understand definitions for common cybersecurity terms and topics.
Hello!
You’re about to visit our web page in English
Would you like to continue?
If this is not what you’re looking for,
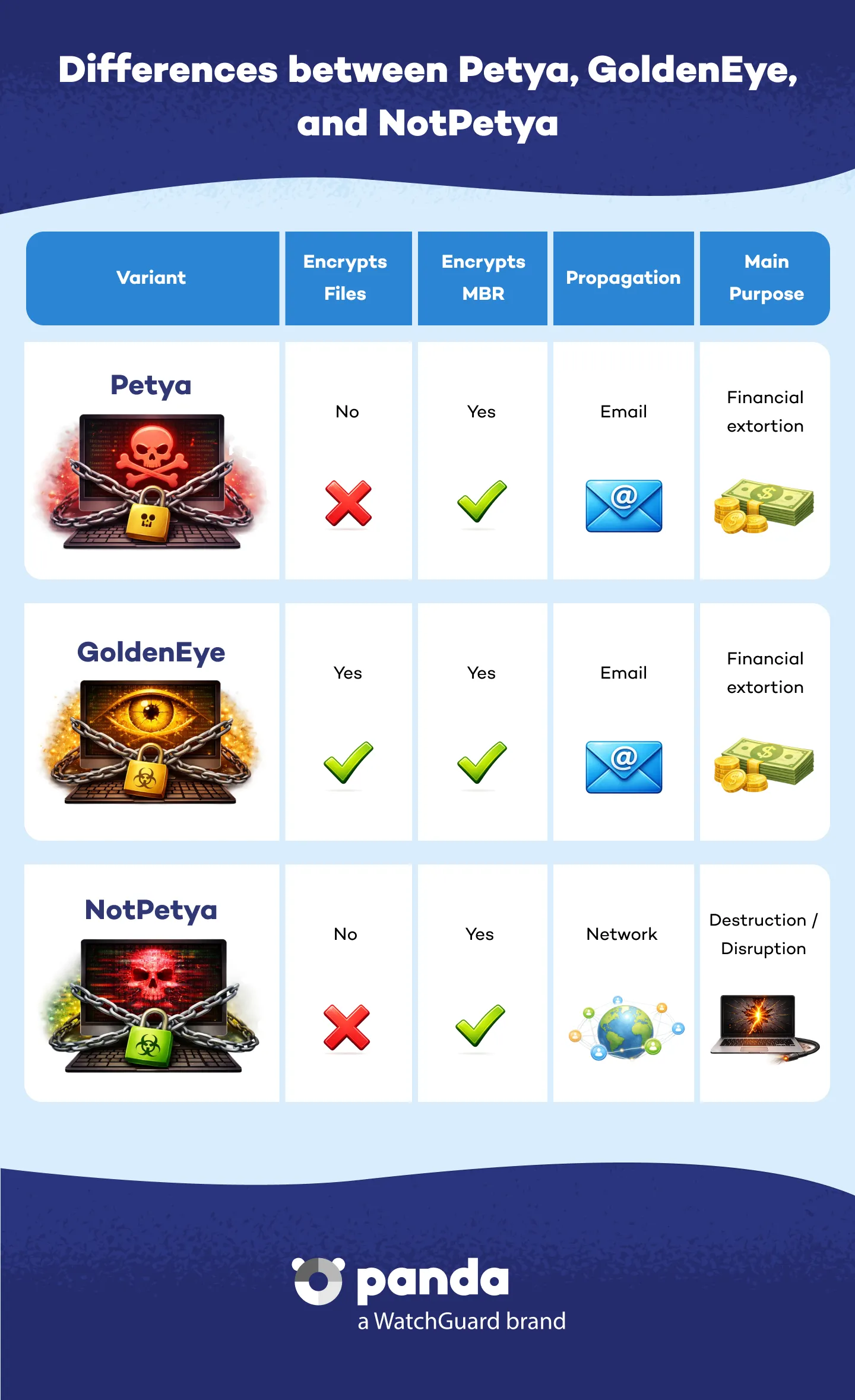
Petya is a ransomware variant that first appeared in 2016 and became known for its massive attacks in 2017 under different names such as GoldenEye or NotPetya. Unlike other ransomware, Petya does not only encrypt files, but renders the system unusable by encrypting the master boot record (MBR), thereby blocking access to the infected device hard disk.
This malware spreads primarily through phishing emails containing infected attachments or through vulnerabilities in outdated operating systems, such as the infamous EternalBlue on Windows systems. After infecting a computer, Petya restarts the system, encrypts the MBR, and shows a ransom note demanding payment in cryptocurrencies to restore the machine to normal use.
Although similar to Petya, NotPetya is even more destructive. This malware spread rapidly in 2017 through a compromised update of the M.E.Doc Ukrainian software. Rather than financial gain, NotPetya was designed mainly for data destruction, which made it a wiper rather than ransomware.
Symptoms include: unexpected reboots, inability to access the operating system, ransom notes with messages in red demanding payment in Bitcoin. It is very important that you do not pay the ransom. Many variants such as NotPetya do not enable data recovery even if payment is made.
Your best defense is an advanced cybersecurity solution such as the Panda Dome product line, combined with good digital practices:
1. Disconnect your device from the network or Internet to prevent the malware from spreading further.
2. Do not pay the ransom. It does not guarantee data recovery.
3. Use a safe boot disk to try to regain control of the system.
4. Contact Panda Security Support.
Yes, although the peak of its activity was in 2017. Many variants remain active and can take advantage of outdated systems. Stay updated on the latest cybersecurity trends and new threats on our Panda Security Media Center blog.
NotPetya’s aim is not to extort money, but cause permanent damage to systems.
Discover the Panda Dome plan that best fits your needs
You can take a look to every single product page (Panda Dome Essential, Panda Dome Advanced, Panda Dome Complete and Panda Dome Premium) or compare all our plans to take a decision.
Digital security is everyone's responsibility. With the right information and tools, you can reduce risks and use the Internet with peace of mind. Explore our guides and protect your online privacy.
Glossary
Easy-to-understand definitions for common cybersecurity terms and topics.
Panda Security Blog
Discover expert advice, detailed tips, and the latest cybersecurity news.

Panda Security, a WatchGuard Technologies brand, offers the most advanced protection for your family and business. Its Panda Dome range provides maximum security against viruses, ransomware and computer espionage, and is compatible with Windows, Mac, Android and iOS.








