Glossary
Easy-to-understand definitions for common cybersecurity terms and topics.
Hello!
You’re about to visit our web page in English
Would you like to continue?
If this is not what you’re looking for,
An exploit is a piece of code or program that takes advantage of a vulnerability or flaw in a computer system, application, network, or hardware. They are typically used to run malicious software, gain unauthorized access, or compromise a system.
Exploits can be developed by researchers for legitimate purposes (proof of concept) or by cybercriminals who integrate them into exploit kits to automate large-scale attacks.
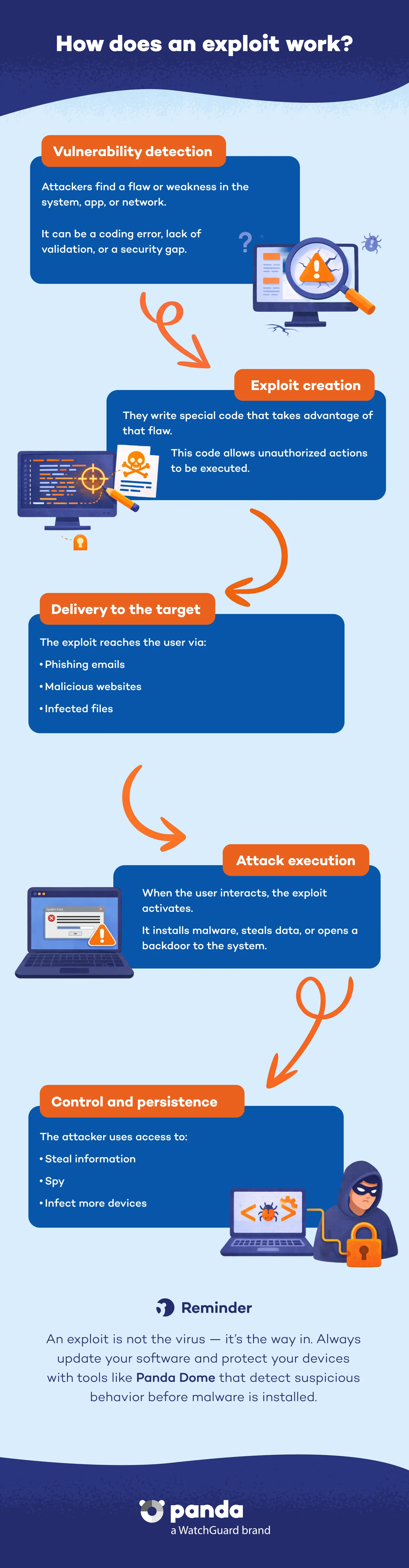
No. The exploit is the piece of code that takes advantage of a vulnerability, whereas the malware is the malicious software that is installed. The exploit is the way malware enters a system.
Traditional antivirus programs protect against known threats. However, against in-memory exploits and advanced kits, you need behavior-based protection such as is provided by Panda Security.
Delaying parches leaves your system vulnerable. EternalBlue demonstrates the impact of an unpatched exploit.
Discover the Panda Dome plan that best fits your needs
You can take a look to every single product page (Panda Dome Essential, Panda Dome Advanced, Panda Dome Complete and Panda Dome Premium) or compare all our plans to take a decision.
Digital security is everyone's responsibility. With the right information and tools, you can reduce risks and use the Internet with peace of mind. Explore our guides and protect your online privacy.
Glossary
Easy-to-understand definitions for common cybersecurity terms and topics.
Panda Security Blog
Discover expert advice, detailed tips, and the latest cybersecurity news.

Panda Security, a WatchGuard Technologies brand, offers the most advanced protection for your family and business. Its Panda Dome range provides maximum security against viruses, ransomware and computer espionage, and is compatible with Windows, Mac, Android and iOS.








