Issue Status |
Symptoms
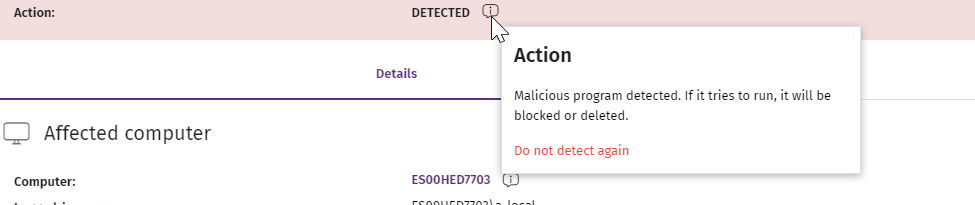
Trj/RansomDecoy.A is detected again after the administrator has selected the Do not detect again action from the detail of a specific malware detection.
Solution
Apply the available hotfix on the affected endpoint.
- Download and save the hotfix file to the endpoint:
hf-wgua2030-ransomdecoydetection.exe - Double-click the downloaded file.
- The hotfix installation does not require restarting the computer. However, under certain circumstances, you may be prompted to restart for the hotfix to be fully applied. If you cannot restart the computer right away, select No when prompted. This postpones the application of the hotfix until the next system restart.
Release Notes
Find all the changes the hotfix includes.
Affected versions
- v8.00.21.X
- From v8.00.22.0010 to v8.00.22.0022 (included)
To see your Adaptive Defense product version, see this article.
File Details
The hotfix updates the following file:
| File name | Location | File Version | Modified Date | Hotfix to be included in future versions? |
| WPDecoy.dll | C:\Program Files (x86)\Panda Security\WAC | 2.1.0.11 | October 18th, 2023 | Later than v8.00.22.0022 |
Verify Hotfix Application
To confirm the correct application of the hotfix, check the file version (in File Details section) or else, verify the values of these Registry keys:
| 32 bits Architecture | 64 bits Architecture | ||
| Registry Key | Value | Registry Key | Value |
| HKEY_LOCAL_MACHINE\SOFTWARE\Panda Software\Setup\Hotfix history\HF_WPDecoy | Revision [REG_DWORD] 6 | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Panda Software\Setup\Hotfix history\HF_WPDecoy | Revision [REG_DWORD] 6 |
| HKEY_LOCAL_MACHINE\SOFTWARE\Panda Software\Setup\Hotfix history\HF_WPDecoy | Result [REG_DWORD] 0 = Success | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Panda Software\Setup\Hotfix history\HF_WPDecoy | Result [REG_DWORD] 0 = Success |