Smartphones play an integral part in our daily lives these days. They carry our personal information, financial details and our connection to the digital world. This makes them a gold mine for mobile data mining, phishing schemes and virus infections.
Today, with more than 4 billion smartphone users in the world, your phone may be vulnerable to digital threats lurking on the internet, with Android users facing particularly high risk. So how do you know if your phone has a virus? Note any signs of suboptimal performance and work through the following guide on how to remove a virus from Android phones.
Can Android Phones Get Viruses?
Android phones can get a virus. As the popularity of smartphones exploded beyond that of computers as personal devices, hackers created new ways to infect and impair them. Unlike traditional viruses, which replicate themselves while running, mobile malware and viruses on mobile devices target weak points within your operating system for data mining, financial gain or network corruption.

Data-sharing capabilities are typically blocked between applications, but some apps have been scrutinized for speculations of mishandling data, making their users increasingly vulnerable to these types of attacks. On top of that, Android phones use open-source code, making them more customizable than other smartphones like iPhones, and therefore easier targets for hackers.
What Malware Can Do to Android Phones
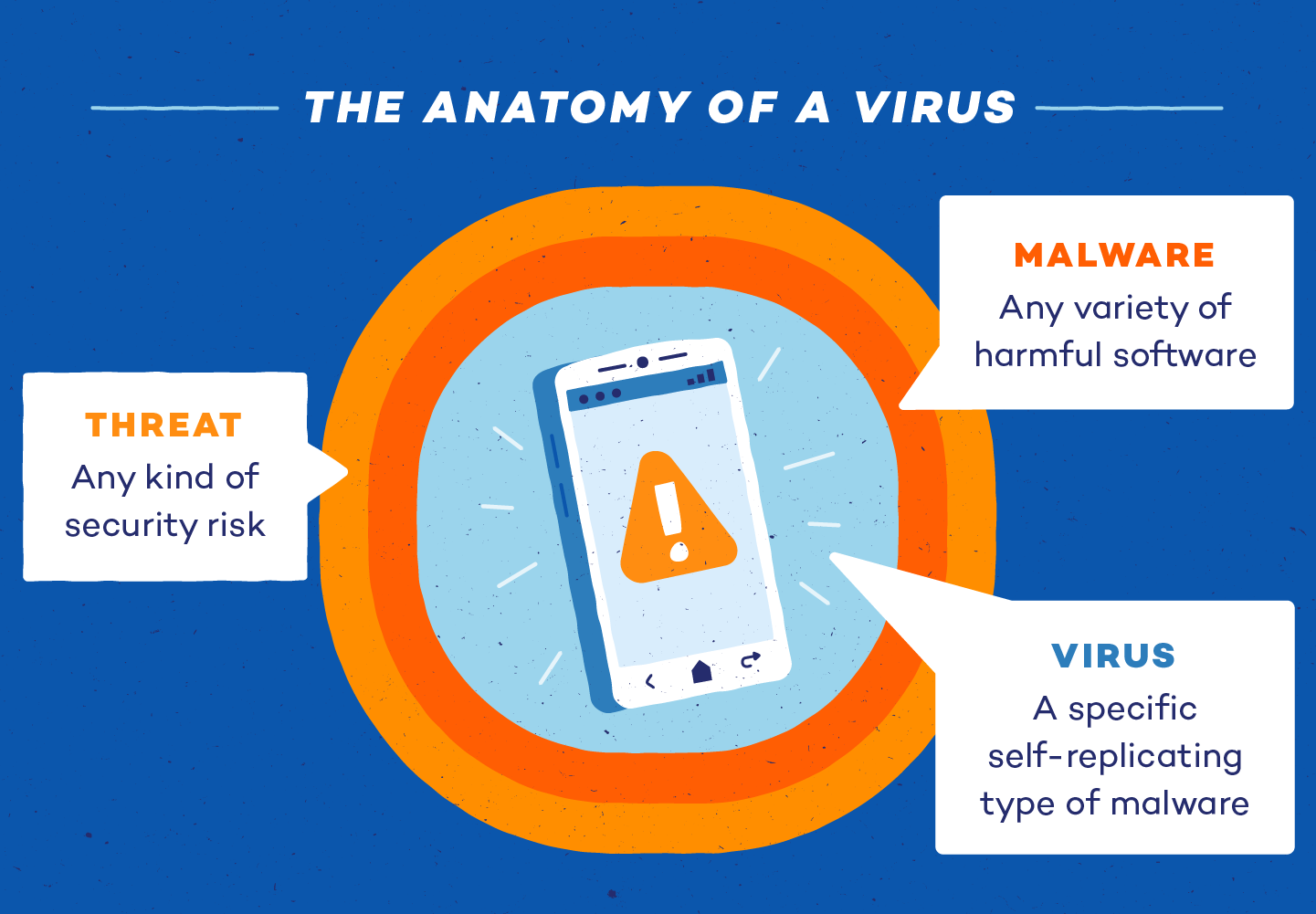
The most common types of mobile viruses targeting Androids are adware, ransomware, spyware, trojan horses, and worms. The term “virus” is now widely used to describe almost any kind of security risk, but it is a specific form of malware.
These harmful programs are designed to gain access to your Android phone, retrieve personal information, increase your data usage and damage the device. Some are even designed to trick you into providing all of that information yourself.
As for where they come from, the internet is a virus’s natural habitat. Legitimate applications, fake emails, infected attachments and many other digital landscapes are perfect grounds for viruses to hide.
Malware can damage an Android phone in many ways. It can affect battery performance, causing the device to overheat and leak data. They can also cause lag and performance issues, nonresponsiveness and random shut-downs.
- Adware: While some pop-ups are an expected part of everyday advertising, an influx can be a sign of adware. At best, it’s an irritation. At its worst, it can track activities and root your device to steal data.
- Ransomware: Ransomware encrypts personal information so the user can’t access it. A ransom is then demanded for files to be released.
- Spyware: Spyware is often attached to seemingly legitimate applications. It then loads itself onto your device to spy on and track your activity, location, usernames and passwords.
- Trojan horse: A trojan horse on your cell phone may appear as a text message. From there, trojans will send messages at a premium, often increasing your phone bill. These types of viruses can also connect themselves to legitimate-looking apps.
- Worm: Another virus spread by texts, a worm doesn’t need user interaction to wreak havoc. Its main goal is to spread to as many devices as possible so hackers can load malware onto your phone and steal data.
9 Signs Your Phone Has a Virus
While many viruses will simply limit the function of your phone, some are created to steal and remove data, transfer malware onto more devices or make unauthorized purchases.
Because mobile malware can run dormant while you use your phone as usual, you may not recognize or know you have a virus immediately. Plus, some suboptimal performance issues are normal symptoms of wear on a phone. However, these symptoms can also be a sign of malicious malware at work.
These nine signs are an indication that your phone may have a virus:
- Excessive data usage: Undetected viruses running in the background of your phone may significantly increase data usage.
- Unauthorized charges: Some forms of trojans may drive up your phone bill with in-app purchases and text charges to premium accounts, which hackers can then collect on.
- Apps crashing: Apps may repeatedly crash if your mobile software is compromised. Before searching for a virus and assuming the worst, check that your storage isn’t full and you don’t have too many apps running simultaneously.
- Unusual search engines: Many people have a primary search engine they use for search queries. If your searches are being answered by new or unrecognizable search engines, this could be a sign that a virus has infected your phone.
- Pop-ups: While some pop-ups are a normal function of advertising while browsing the web, if your browser is closed and you’re experiencing increased pop-ups, you may be experiencing adware, a type of malware whose goal is data mining.
- Increased battery drain: You may experience an inexplicably quick drain on your battery with the increased use of your phone’s RAM if a virus is running in the background.
- Unrecognizable apps: When you see unrecognizable or fake apps that were mysteriously downloaded, they may be malware. Trojan horses can also attach themselves to legitimate applications and cause further damage.
- Overheating: Malware can consume RAM and CPU quickly, causing your phone to overheat. While occasional overheating may be normal, a chronic issue could be a signal that there’s something more dangerous afoot.
- Fraudulent linking: Malware may gather sensitive data and attempt to infect your contacts by sending dangerous links and attachments through texts, emails or social media messages.
How to Remove a Virus From an Android Phone
Android phones have more potential for customization. Because of its open-source code, Android devices are very easy to access and manipulate on a software level. This makes them vulnerable to malware attacks. Antivirus software is the most fail-safe way to protect your Android from viruses in the first place. However, there are four simple steps to remove a virus from an Android phone.

Here’s how to remove malware from Android devices:
Step 1: Clear the Cache
The first item on your checklist is your browser. If you visited suspicious sites, some data will still be stored. Navigate to settings and select Apps & notifications. Next, find your browser of choice (in our example, we use Chrome). Go to its storage and select Clear cache.
Step 2: Reboot the Device
Press and hold the power button. When the dialogue box appears, choose reboot to safe mode. The term “safe mode” should appear in the corner of your screen after rebooting.
Step 3: Find Suspicious Apps
Open your settings. Select Apps. Tap See all apps and enter Installed apps in the dropdown menu. Manually review applications to find any suspicious downloads. Once identified, open the app information and uninstall or force close it. After this step, you can restart your phone like normal.
Step 4: Enable Play Protect
The most secure way to protect an Android against a virus is by installing an antivirus, but Play Protect can be used as a secondary protection measure. To enable this built-in software, enter the Google Play Store app and open the menu under your avatar. Choose to activate Play Protect so it can scan your device for security threats.
As a last resort, you can wipe your device and reset it to its factory settings. If this is your only choice, make sure all of your important documents, pictures and information are backed up to a more secure device or the cloud.
While security measures like Play Protect reduce the chances of malware infiltrating your Android, it’s best to use an antivirus so that your device is actively monitored and protected around the clock.
How to Check for Malware on Android Phone
Like vulnerability assessments for large infrastructure systems, it’s important to scan your smartphone for viruses regularly. While many viruses may make your phone act differently than normal, sophisticated viruses can often go virtually undetectable to the naked eye. Here’s how to see if your phone has a virus:
1. Run Regular Scans
Routine scans ensure there’s no unauthorized access or signs of malware on your phone. Installing an antivirus can be the difference between a fancy Android and a plastic brick. Make sure to routinely scan for any strange activity.
2. Check for Suspicious Apps
Go through your installed apps and confirm you recognize all of them. Sometimes, malware is embedded in the form of applications. Uninstall any apps you don’t recognize as quickly as possible before they cause any damage.
3. Examine Battery Usage
It’s fair to say that battery performance is a very common issue with modern smartphones. Just as it could be a sign of wear and tear, it can also indicate that malware is present. Examine your battery usage and see if it fits your screen time.
4. Monitor Data Usage
Some malware manipulates the amount of data you use by running programs in the background that could bleed your data plan dry. Check your data usage for unexplainable activity and see if you can pinpoint which app it’s coming from.
5. Check Phone Performance
Go through your phone’s performance in settings and consider whether any strange behavior is a sign of an aging Android phone or malware. If this behavior has increased gradually over time, it’s likely the former; if it came on suddenly, do some further investigating.
If you have suspicions your phone may have a virus, removing it and investing in security systems should be a priority. While it may be necessary to wipe and restore your device if the virus is dangerous enough, there are simpler restoration techniques.
How to Remove a Virus From an iPhone
Wondering how to know if your iPhone has a virus?While the Android system is open-source, the iPhone operating system is fairly secure, making it less likely for malware to infiltrate an iPhone than an Android phone. But viruses can still break through closed-coded systems, especially on jailbroken iPhones. If your iPhone does manage to become infected by a virus, there are three steps you can take to remove the virus.
Step 1: Clear Your Browsing Data and History
First, select Settings. Then choose your primary browser and clear its history and website data. If you regularly use any other browsers, repeat this process for them, too.
Step 2: Restore a Backup Version of Your Phone
Navigate to your phone’s settings, your Apple ID, and then the iCloud. Here, you should select Manage Storage, then Backups. Choose and restore the device to the most recent backup.
Step 3: Reset Your Phone to Its Factory Settings
This option should only be used as a last resort. Open your settings, choose General, find Transfer or Reset iPhone, and choose Erase All Content and Settings. Your phone will be reset to its factory settings.
Resetting your iPhone to its factory settings should always be the last remedy you try since you’ll lose access to any data or files that don’t have backups. Before this, follow the first two steps to remove a virus, install any iOS updates or download additional antivirus software for Mac and iOS devices to help protect your phone from hackers.
9 Tips to Protect Your Phone Against Viruses
Now that you know how to get rid of malware on Android, you can prioritize safe and secure browsing habits going forward.As the first line of defense, antivirus software can protect your phone against malware. If all else fails, regularly backing up your phone will ensure you have a previous version to restore as a fail-safe. However, there are other steps you can take to protect your phone from a virus infection before resetting it becomes an option.
1. Only download verified apps: There’s no need for you to be patient zero. Avoid third-party app stores and only download apps from verified sources like the Google Play Store or the App Store. Doing so minimizes the risk of installing dangerous apps posing as legitimate software. Always verify the source of the application before installing it.
2. Use secure Wi-Fi networks: Always use protected Wi-Fi or a VPN. Making sure your data is transferred using HTTPS and installing additional security systems deters hackers from interrupting the data flow to and from your phone.
3. Check app permissions: Before downloading an unfamiliar app or allowing it to connect with other apps in your digital sphere, read its terms and conditions. Permission to access personal information, including contacts, or change the terms without notice should never be automatic.
4. Install antivirus software: Antivirus software is the best line of defense against mobile malware. Run the software regularly and remove any threats detected.
5. Update your OS: Operating system updates often patch bugs found in its previous versions. Make sure your phone is always on the latest version.
6. Don’t open suspicious messages: Malware can come in the form of email attachments, texts and links. Don’t click unfamiliar links or messages, as they may be a gateway to phishing sites.
7. Don’t jailbreak your phone: Staying rooted allows necessary updates and patches to your operating system to be installed when they are released. When you jailbreak your phone, you’re vulnerable to holes found in previous versions and the dangers open-source code can pose.
8. Keep passwords secure: Use a password generator to help add a bit of variety to the passwords you use for applications and devices that store your data.
9. Clear your browsing and data history: Clearing your browser and data history can remove suspicious links that may be compelling and unfamiliar.
Some viruses on cell phones are dormant until activated to infiltrate as much user data as possible before being detected. Antivirus software can protect your mobile devices against cyberattacks, and installing an Android VPN on your mobile device can offer additional protection from the instability of open-source codes.
If you’re wondering how to clean your phone from a virus for free, Panda’s suite of digital security solutions can help you monitor your device around the clock. Stay vigilant when downloading new software to your devices, and understand the performance issues that may be associated with symptoms of mobile malware at work.
Virus on Android FAQ
The flexibility and high level of customization Android phones provide to users is unrivaled. However, it trades in a measure of security in exchange for that open-source nature. A well-informed hacker could overcome its defenses — but a well-informed user could sidestep the issue with the right tools.
Can I Scan My Phone for Viruses?
Yes, regularly scanning your Android phone for viruses and other malware is a crucial step in maintaining your device’s security. In fact, each Android device comes with a built-in security feature called Google Play Protect that can automatically scan apps on your device.
Check your settings to ensure Scan apps with Play Protect is turned on. You can also manually initiate a scan by opening the Google Play Store app, tapping your icon in the top right and selecting Play Protect. You’ll receive a status report, and you can also run a new scan by tapping the Scan button. This precaution can catch a virus on Samsung phone operating systems before it does irreparable damage.
What Android App Removes Viruses?
A good antivirus app can identify and quarantine viruses and digital threats. For example, Panda’s Antivirus for Android is a trusted phone virus cleaner that monitors your device in real time and routinely checks for any malware presence. Visit the Antivirus for Android product page to learn more about the best malware removal Android has to offer.
Will Resetting an Android Phone Remove a Virus?
Yes, resetting an Android phone to its factory settings will remove all data installed, including viruses, suspicious apps and unwanted browser data. This is the most efficient method but is recommended as a last resort.
How Do You Get Viruses on Your Phone?
You can get viruses on your phone from browsing online and visiting suspicious sites or clicking on pop-ups, texts and suspicious links. You can also get viruses from downloading non-trusted apps and documents.
Can You Get a Virus on Your Phone by Visiting a Website?
Yes, it is possible to get a virus or other malware on your phone by simply visiting a malicious website, although it’s less common than installing a compromised app. This can happen through what are known as “drive-by downloads,” where malicious code is automatically downloaded and installed onto your device without your explicit consent or knowledge, simply by loading the page.
More frequently, however, visiting a suspicious website can expose you to phishing attempts, unsolicited pop-ups (adware) or trick you into clicking on malicious links that then download malware. Always exercise caution with unfamiliar websites and ensure your browser and operating system are up-to-date to combat known vulnerabilities.
How Can I Protect My Mobile Devices from Malware?
Aside from the obvious (like not opening suspicious messages, attachments or links), there are a few more ways to protect yourself from smartphone malware on an Android:
- Do not connect to unsecured Wi-Fi.
- Routinely clear your browsing history.
- Only download verified applications and always check app permissions.
- Ensure your phone is on the latest available version of its operating system.
How Do You Remove a Virus from a Samsung Phone?
Removing a virus from a Samsung phone follows the same general steps as removing a virus from any other Android device, as Samsung phones run on the Android operating system. The process involves clearing your browser cache, rebooting your device into safe mode to isolate the malicious software, manually finding and uninstalling any suspicious applications and finally, enabling or ensuring Google Play Protect is actively scanning for security threats. In severe cases, you can try a factory reset as a last resort. Always consider installing a reputable antivirus app for proactive protection on your Samsung device.
While Android settings don’t offer a direct “virus scan” button, you can effectively check for signs of a virus by observing changes and reviewing information available within your phone’s settings.
Here’s how to check if your phone has a virus in settings:
- Unusual data usage: Navigate to Settings > Network & internet > Data usage to see if data consumption is unexpectedly high, which could indicate malware running in the background.
- Excessive battery drain: Check Settings > Battery > Battery usage (or similar) to identify apps consuming an unusual amount of power, especially if you don’t recognize them or they appear to be running constantly.
- Suspicious apps: Go to Settings > Apps (or Apps & Notifications) and review your See all apps list for any applications you don’t recognize or didn’t intentionally install. These could be malicious.
- Google Play Protect: Ensure this built-in security feature is enabled. Open the Google Play Store, tap your profile icon and select Play Protect. Here, you can confirm it is active and manually run a scan.
What to Do If You Have a Virus on Your Phone?
If you suspect a virus on your phone, take immediate action to stop the damage and remove the threat. Here’s what to do if you have a virus on your phone:
- Disconnect from the internet: Turn off Wi-Fi and mobile data immediately to prevent the virus from spreading or sending out your data.
- Clear your browser cache: Go to your browser’s settings and clear its cache and data. This can remove malicious scripts or downloaded components.
- Reboot into Safe Mode: This mode prevents third-party apps from running, allowing you to isolate and remove the virus. Press and hold the power button, then tap and hold the Power off option to make the Reboot to Safe Mode prompt appear.
- Identify and uninstall suspicious apps: In Safe Mode, go to your phone’s settings (Apps or Apps & Notifications) and look for any unfamiliar or recently installed apps. Uninstall them.
- Run Google Play Protect: After removing suspicious apps, reboot normally and then open the Google Play Store, go to Play Protect and run a full scan.
- Install a reputable antivirus app: For ongoing protection and a thorough scan, download and install a trusted antivirus application from the Google Play Store.
- Change passwords: If you suspect data compromise, change passwords for all important accounts (email, banking, social media).
- Factory reset (last resort): If the virus persists or your phone remains unstable, a factory reset will wipe all data and return your phone to its original state, effectively removing even stubborn malware. Remember to back up important data beforehand if possible.
Sources: Threat Insight Report | IDG | Khalifa University | University of Cambridge | Hong Kong University






4 comments
So if a phone get a virus does that mean u lose all your personally data and everything u lose
Someone is threating to put a virus on my phone am so scared right now but thank for the knowledge. I hope it works
I am glad that I have been informed of the parasite
No, it fucking wont come out of your phone with a factory reset, just like the computer virus that came with it.. WHILE I HAD PANDA ON BOTH