Fake apps look like the real thing but are actually designed to steal your personal info or cause harm to your device. They trick you into downloading them by mimicking trusted apps.
We all rely on our smartphones to make life easier, but as more people use mobile apps, cybercriminals are finding new ways to target us — especially through fake apps. These apps, like fake websites, may look just like the real deal, but once downloaded, they can steal your data, install malware or cause other problems on your device.
We’ll show you how to spot these fake apps and what you can do to stay safe. You’ll learn about the risks they pose, warning signs to watch for and simple tips to keep your personal information protected.
What Are Fake Apps?
Fake apps are malicious or counterfeit applications that deceive you into believing they’re legitimate. Often mimicking popular apps or services, these fraudulent programs are distributed through unofficial app stores, phishing links or even sometimes legitimate platforms before detection.
Their primary goal is to exploit unsuspecting users by stealing personal information, infecting devices with different types of malware or facilitating unauthorized transactions.

How Do Fake Apps Work?
The process of creating and distributing fake apps is unfortunately easy to carry out — a cybercriminal can simply register themselves as a developer on any app store, download a legitimate application and rewrite it to include malicious code.
To deceive users, these fake apps often mimic the branding, functionality and design of trusted, well-known apps. From logos and color schemes to user interfaces, they can appear nearly identical, making it difficult to distinguish between the fake and the original.
Once uploaded to an app store, cybercriminals may boost credibility by adding fake reviews or mimicking download statistics. The malicious payloads hidden in these apps can range from spyware to ransomware to heuristic viruses, aiming to steal sensitive data, gain unauthorized access or damage devices.
Common Threats From Fake Apps
Fake apps pose numerous risks, ranging from financial losses to compromised personal data. Here are some of the most common threats associated with fake apps:
- Data theft: Fake apps often aim to steal sensitive user information, such as login credentials, payment details and personal data. This stolen information can be sold on the dark web or used for unauthorized transactions.
- Malware and viruses: Many fake apps contain malicious code designed to infect devices with malware or viruses. These programs can cause system disruptions, corrupt files or serve as a gateway for further attacks on your device.
- Ad fraud: Fake apps can use malvertising or generate fraudulent ad clicks, earning revenue for cybercriminals at the expense of advertisers. This drains marketing budgets and undermines the effectiveness of legitimate ad campaigns.
- Phishing attacks: Some fake apps are designed to imitate login screens or request sensitive data under the guise of legitimate requests.
- Identity theft: By accessing personal details such as names, addresses and ID numbers, fake apps enable criminals to impersonate users, opening fraudulent accounts or engaging in illegal activities in the victim’s name.
- Ransomware: Certain fake apps can lock you out of your devices or data, demanding payment in exchange for access. This not only disrupts personal and business operations but also risks financial loss without any guarantee of recovery.
- Spyware: Fake apps may covertly monitor your activity, capturing keystrokes, screen activity or GPS locations. This information can be used for blackmail or to compromise additional accounts.
- Trojans: These apps act as deceptive tools, appearing harmless while providing unauthorized backdoor access to attackers. Once inside a system, they can facilitate extensive data breaches or network infiltration.
- Unnecessary subscriptions and hidden charges: Fake apps may trick you into subscribing to expensive, unnecessary services or charge hidden fees without clear disclosure.
Types of Fake Apps
There are a variety of categories that fake apps fall into depending on the malicious intent a cybercriminal has when creating them. Malware is any code that puts a user, a user’s data or a user’s device at risk. The type of malware injected into a fake app can vary by function and capability, and it may fall into any of the following categories.

New H3: Fake Banking Apps
Fake banking apps mimic legitimate financial institutions to steal sensitive information, such as login credentials and account details. These apps can also facilitate unauthorized transactions, resulting in direct financial loss for users.
New H3: Fake Gaming Apps
Fake gaming apps entice users with promises of free or exclusive games but often contain malware, adware or spyware. They may also trick you into making in-app purchases that deliver no value.
New H3: Fake Dating Apps
Fake dating apps exploit the popularity of online dating platforms to steal personal information or lure you into phishing schemes. Some may also serve as a gateway for spyware or unnecessary subscription charges.
New H3: Fake Messenger Apps
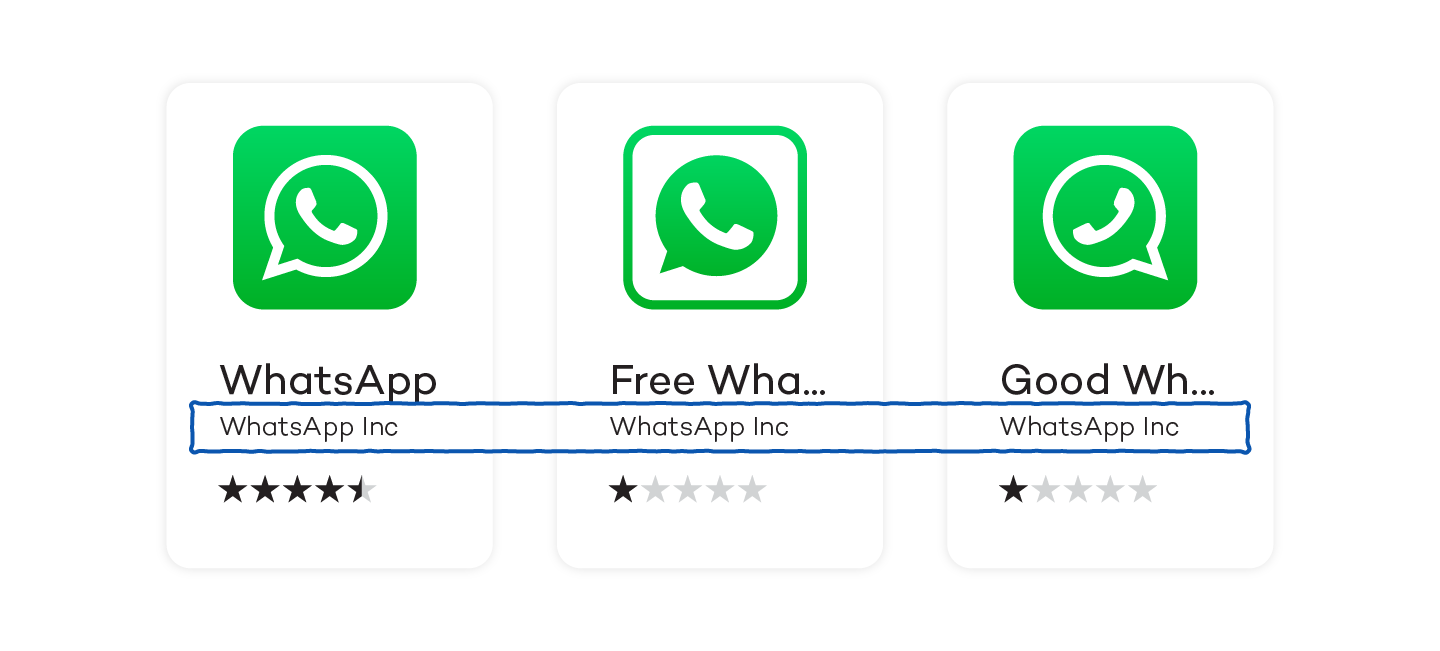
Fake messenger apps replicate popular communication platforms like WhatsApp to harvest sensitive conversations, contact lists or login credentials. These apps can also distribute malicious links, putting you and your networks at risk.
Billing Fraud Apps
Billing fraud involves apps that automatically charge purchases to a user’s phone bill without the user’s consent. This may include sending premium SMS messages, making collect phone calls or making purchases in an app store.
Hostile Downloaders
Hostile downloaders don’t contain malicious code themselves, but they initiate the download of other harmful applications onto a device without your knowledge.
Phishing Apps
Phishing apps often appear to be from a trusted source and request your authentication credentials or billing information, which is then sent to third parties. These apps often target bank information, credit card numbers, online account information and login credentials.
Ransomware Apps
Ransomware apps take partial or extensive control of your device by encrypting your data. To decrypt your data, they will ask you to make a payment or perform certain (often transactional) actions. Common instances of this include locking you out of your device and demanding money before you can regain access.
Rooting Apps
Rooting apps contain code that roots the device, commonly known as jailbreaking. Not all rooting apps are harmful, and many legitimate apps perform rooting — but legitimate apps always require user consent and don’t execute harmful actions against your device.
Spam Apps
Spam apps often gain access to your contact list, sending spam messages to friends, family or colleagues without your knowledge. In some cases, they also use the device to send bulk emails, contributing to broader spam operations. This not only disrupts recipients but also risks your email address or phone number being flagged as a source of spam, potentially leading to account restrictions or reputational damage.
Spyware Apps
Spyware apps send personal data to third parties without your consent. Exploited data may include text messages, call logs, contact lists, email records, photos, browser history or data from other apps on the user’s device.
10 Ways to Spot Fake Apps
With over 34 billion app downloads globally in the first quarter of 2024, the mobile app market remains a prime target for cybercriminals — Google Play malware alone accounted for 600 million downloads in 2023.
The best defense against fake apps is knowing how to spot them. By carefully vetting apps and watching for key warning signs, you can significantly reduce your risk of downloading malicious software.
1. Read the Reviews
Reading an app’s reviews is a great way to discover any potential issues other users have already reported. If you notice multiple negative comments or complaints, tread with caution before downloading the app onto your device.

Take a closer look at the positive reviews as well. Cybercriminals know that ratings and reviews play a big part in the number of downloads an app may get, and may generate fake reviews to lure victims. Take any positive reviews with a dose of skepticism.
2. Check the Developer
Always take a little extra time to do some research on the developer of any app you’re thinking about downloading. A quick Google search can let you in on a developer’s reputation and whether or not they’re a trusted source.
Fake app developers are also known for giving apps the same name as their genuine counterparts, sometimes changing a letter or two in the hopes of it going unnoticed. Read each letter carefully and look out for any misspellings, which could tip you off to a potential fake app.
3. Check the Release Date and Update Frequency
Take note of the date listed for when an app was released. If you come across a recently published app with a high number of downloads, it’s a strong sign of a fake app. Most apps that have gained popularity and a high number of downloads have been on the market for a while.
4. Pay Attention to Permissions
Fake apps tend to ask for extra authorizations they don’t actually need, but this often goes unnoticed as most people don’t take the time to read the fine print. Always verify whatever authorizations an app requests to perform on your device before allowing full access.
5. Examine the App’s Design and User Interface
Fake apps often lack the polish and quality of legitimate apps. Pay attention to clunky designs, poor-quality images and inconsistent branding, which could indicate the app is not genuine. Legitimate apps from reputable developers usually invest in a smooth and professional user experience.
6. Look for In-App Ads or Redirects
Fake apps frequently bombard users with excessive ads or redirect them to external websites. These tactics are often used to generate revenue or lead you to phishing sites. If an app has an overwhelming number of ads or suspicious redirects, it’s likely fraudulent.
7. Search for the App Online
Perform a quick online search for the app’s name along with terms like “reviews” or “legitimacy.” Or type: Is XYZ app legitimate? Legitimate apps often have a significant online presence, including official websites or mentions in credible articles, while fake apps tend to lack this footprint.
8. Check the App URL
Examine the URL of the app on the store carefully. Fake apps may use URLs that look similar to the original but include subtle changes, such as extra characters or misspellings. Ensure the URL matches the official name of the app and developer.
9. Look for Too-Good-To-Be-True Offers
Fake apps often lure users with unrealistic promises, such as free premium features or exclusive rewards. Be cautious of apps offering deals that seem too good to be true, as they’re often a red flag for malicious intent.
10. Look for Spelling and Grammar Errors
Poorly written app descriptions, titles or instructions are a common sign of a fake app. Legitimate apps are typically reviewed for quality and professionalism, whereas fake apps may rush through the content, resulting in noticeable errors.
How to Protect Yourself From Fake Apps
As mobile technology continues to evolve, so do the tactics of cybercriminals targeting users through fake apps. By adopting a few proactive security measures, you can significantly reduce your risk of falling victim to these threats.
- Enable two-factor authentication (2FA): Add an extra layer of security by enabling 2FA on your accounts. This ensures that even if your password is compromised, a secondary verification step is required to access your account, protecting sensitive data such as banking information.
- Regularly update your software: Keep your device’s operating system and apps up-to-date. Regular updates fix vulnerabilities that hackers may exploit, reducing your risk of attack. Always download updates directly from your device settings — never from unverified sources.

- Read app permissions carefully: Before installing an app, review the permissions it requests. Be cautious if an app asks for access to data or features that seem unnecessary for its functionality, as this could indicate malicious intent.
- Use antivirus software: Install reputable mobile antivirus software to monitor and block threats in real time. These tools can automatically detect malicious apps and protect your device from a wide range of cybersecurity risks.
Keeping modern online threats and advancing fake apps in mind, antivirus protection might not be enough — you may want to use anti-malware to further strengthen your online security.
Safeguard Your Personal Information With Panda Antivirus
Protecting your personal information is more important than ever, and Panda Dome makes it easy to stay secure. With its real-time scanning and powerful security features, Panda Security helps keep your devices safe from fake apps and malware.
Plus, if you’re running a business, Panda’s business antivirus features offer robust protection for your company’s data, ensuring both personal and professional security are always top priority.