Ransomware is malicious software that infects our equipment, and gives cybercriminals the ability to lock your PC from a remote location and encrypt your files grabbing control of all information and data stored. To unlock the virus, it launches a popup window that asks us for ransom in the form of a payment, such payment is usually made in virtual currency (bitcoins for example).
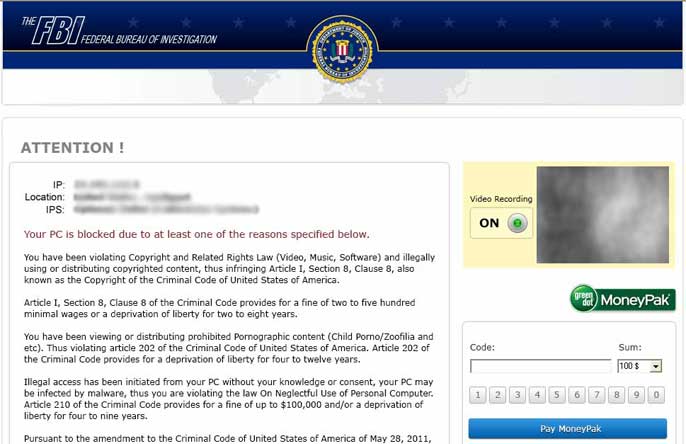
One of the most famous Ransomware is the Police Virus. When affected, it blocks the infected computer and sends a message pretending to be the National Police. It would state that since the team has detected illegal activity related to pedophilia and pornography. To regain access to all information, the malware asks the victim to pay a ransom in fines.
The shame, the need to recover information, and the pressure from an alarming, unknown message, are some of the factors that provoke some of the people to pay for the rescue of their computer. Hackers are seeing a lot of opportunities behind this behavior and bring up infection-driven business models using ransomware. At Panda Security we want to give you the keys to recover your infected computer without paying anything.
How Does Ransomware Work?
It camouflages within another file or program appealing the user to want to click: email attachments, videos from pages of doubtful origin or even system updates from reliable programs like Windows or Adobe Flash.
Once you have downloaded it to your computer, the malware is activated and causes blocking of the entire operating system and launches the alert with the threat and the amount of “rescue” to be paid to retrieve all information. The message may vary depending on the type of ransomware that we face: pirated content, pornography, false virus…
To enhance the uncertainty and fear of the victim, sometimes included in the threat is the IP address, the company providing internet, or even a photo captured from the webcam.
How to Avoid Ransomware?
Practices to avoid being infected are common to the same rules we must follow to avoid other viruses:
- Maintain an updated operating system to avoid security breaches
- Install a good antivirus product, and always keep it updated
- Do not open emails or files from unknown senders
- Avoid surfing unsecure pages or unverified content
- Always have an updated backup, it is the best way to avoid loss of information
How to Disinfect a Computer Affected by Ransomware
If despite taking all reasonable steps, your computer is under attack of Ransomware, Panda Security can help you disinfect your computer and retrieve all your information.
On this page you have the steps to disinfect the Police Virus.
If the ransomware that affects you is one of the other forms, we recommend you contact our Technical Support and they will give you the steps to regain control of your computer.






