Have you ever wondered how the message you send on your cell phone makes its way to your friend’s computer? While we may not consider this to be communication in the typical sense, that’s exactly what it is. An IP address helps internet-based devices ensure their messages are sent to and from the correct place.
But what is an IP address? Internet protocol — or IP — dictates how devices communicate with each other, and IP addresses identify internet-based devices. All network and internet devices use IP addresses to send and receive messages. In fact, some of your at-home security protocols are designed to specifically protect these addresses!
This guide will explain what an IP address is, who can access them, how to protect them and more.
What Is an IP Address?
An IP address is a unique string of figures that identifies internet and network devices. Without an identifier, a device is unable to send or receive messages and its location is untraceable.
Even though IP addresses are used as a measure of internet security, they can still reveal portions of your geolocation, including:
- Zip codes
- Area codes
- Cities
- Internet service provider (ISP) names
However, an IP address will only reveal the geolocation of where your IP address is assigned and used, and it will protect your full name and address.

How Are IP Addresses Assigned?
IP addresses are assigned by internet service providers and the Internet Assigned Numbers Authority (IANA). The IANA is part of the Internet Corporation for Assigned Names and Numbers (ICANN), which is a nonprofit dedicated to maintaining internet security.
IP addresses are not random, even if they are dynamic. They can be changed or reassigned at any time by an ISP. Additionally, users can request an IP address change directly from their ISP.
How IP Addresses Work
Just like any other communication technique, devices want to send and receive information. IP addresses help determine which other internet-based devices can communicate. There are four steps to this communication process:
- Connect: Devices must connect to the internet. To do this, they connect to a network that has an internet link. This could be an at-home ISP or a company network.
- Assign: The ISP and IANA assign each device an IP address.
- Use: Devices use the internet to communicate. All activity goes through the ISP and is then routed back to the original device.
- Reassign or change: While not a required step, IP addresses can change or be reassigned. Turning a modem or router on and off can reset an IP address, or an ISP can reassign one if necessary. Additionally, home IP addresses do not travel with devices. These devices — whether connecting to the internet at a coffee shop, airport, hotel or other location — will receive a new, temporary IP address depending on the network they use to communicate.
If a device is unable to connect to the internet, it will be unable to access its IP address and communicate with other devices.
Types of IP Addresses
There are two types of IP addresses: public and private. These identifiers have distinct times and places where they are used, but they both help devices identify and communicate with other devices and their networks.
Public IP Addresses
Public IP addresses are the primary identifiers assigned to an entire network by an ISP. These addresses are then used by outside devices to recognize your entire internet network. Public IP addresses come in two forms:
- Static IP addresses: Static IP addresses do not change. These are crucial for individuals and businesses who wish to host their own server. Static addresses guarantee that websites and email addresses connected to a server are consistently available to other devices.
- Dynamic IP addresses: Dynamic IP addresses change consistently over time. An ISP may reassign IP addresses and recycle older identifiers to save time and money while also providing additional security. Because they change or are reassigned regularly, dynamic IP addresses are more difficult for hackers to track, hack and exploit.
For those who don’t host their own server — including networks that utilize dynamic identifiers — there are two types of website IP addresses:
- Shared IP addresses: Shared IP addresses are assigned to websites that are hosted on the same server by the same web hosting provider. Most of these sites are fairly simple with manageable website traffic.
- Dedicated IP addresses: Some web hosting platforms may purchase dedicated IP addresses that can then be assigned to specific sites. These help simplify SSL certificate purchases, file sharing or transferring and website access.
Private IP Addresses
Private IP addresses are only generated within a network. For example, your at-home router and ISP create and assign private IP addresses to all of the devices that connect to your home network. These include devices like cell phones, laptops, tablets and Internet of Things devices like smart thermostats and fridges. These identifiers will only be used within your network and are designed to help your router recognize and organize your at-home devices.
Public vs. Private IP Addresses
| Public IP Addresses | Private IP Addresses |
|---|---|
| Generated outside a network | Generated inside a network |
| Assigned by an ISP to a router | Assigned by ISP and router to individual devices |
| Point to an entire network | Point to individual devices inside a network |
| Can be dynamic or static | |
| Website IP addresses can be shared or dedicated |
IPv4 vs. IPv6
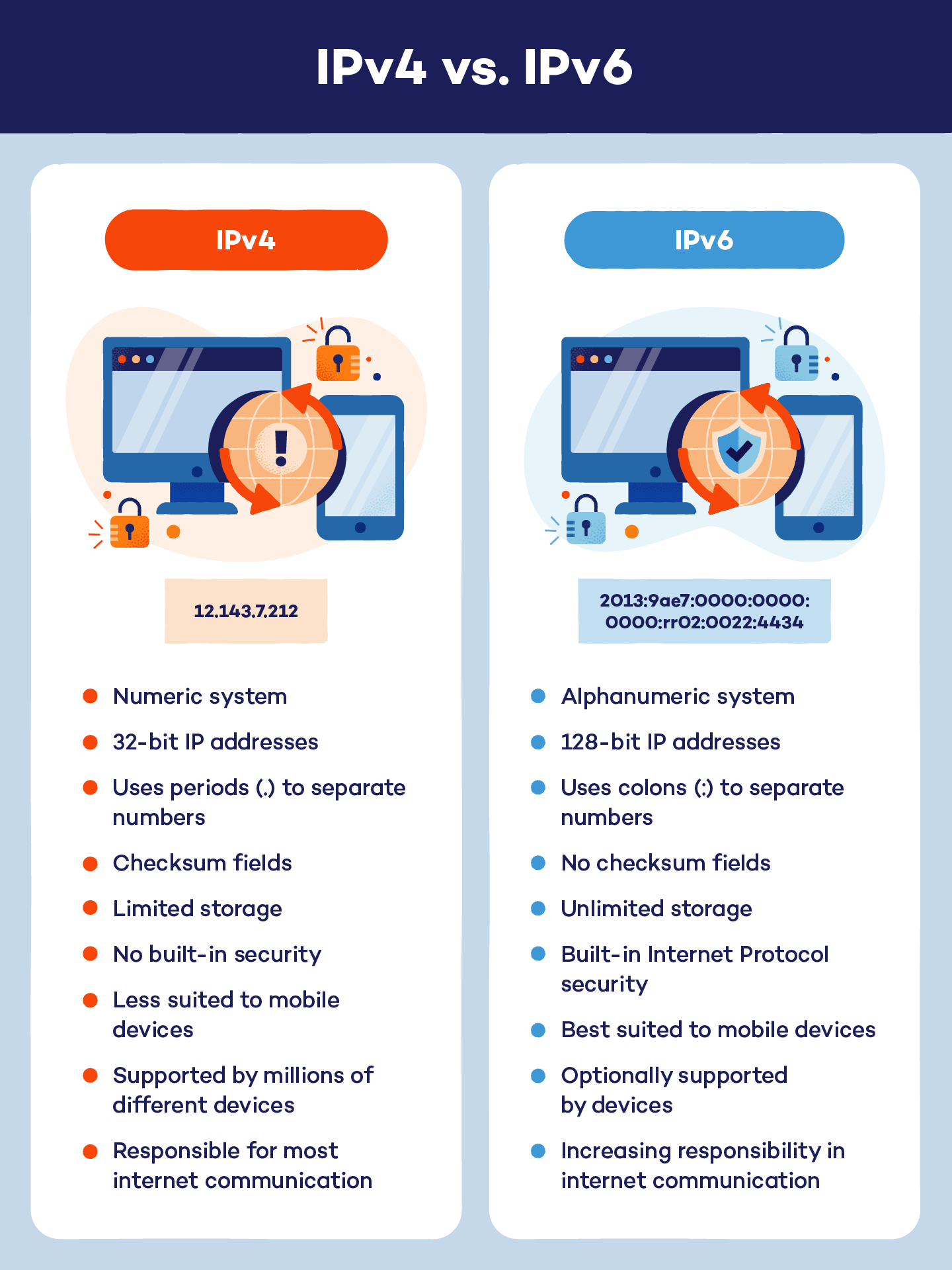
There are two IP address versions: IPv4 and IPv6. While IPv4 is the more common system for creating IP addresses, they are both used for device connection and communication.
IPv4
IPv4 is the original device identifier and Internet Protocol system. IPv4 was established in 1983, and its numeric system can carry more than 4 billion different addresses. Currently, IPv4 is responsible for the majority of communication across the internet.
IPv4 addresses are formatted as a set of four numbers separated by periods. Each number in a set can range from 0 to 255, so the IP address range is 0.0.0.0 to 255.255.255.255. For example, an IPv4 address could look like: 12.143.7.212.
IPv6
IPv6 is the most recent version of the device identifier and Internet Protocol system. Sometimes referred to as IPng — Internet Protocol next generation — this newer system was originally issued in 1994 and is being used to cover the need for more internet identifiers.
IPv6 addresses use both letters and numbers to create more than 340 undecillion identifiers. These addresses use colons to separate multiple groups of numbers and hexadecimals. For example, an IPv6 address could look like: 2013:9ae7:0000:0000:0000:rr02:0022:4434.
How Can You Find Your IP Address?
Finding your public IP address can be as simple as typing “what is my IP address” into a search engine. Your public address will show at the top of the results page, but your device’s geolocation should not be included in these search results.
Finding your private IP address depends on the device you’re using.
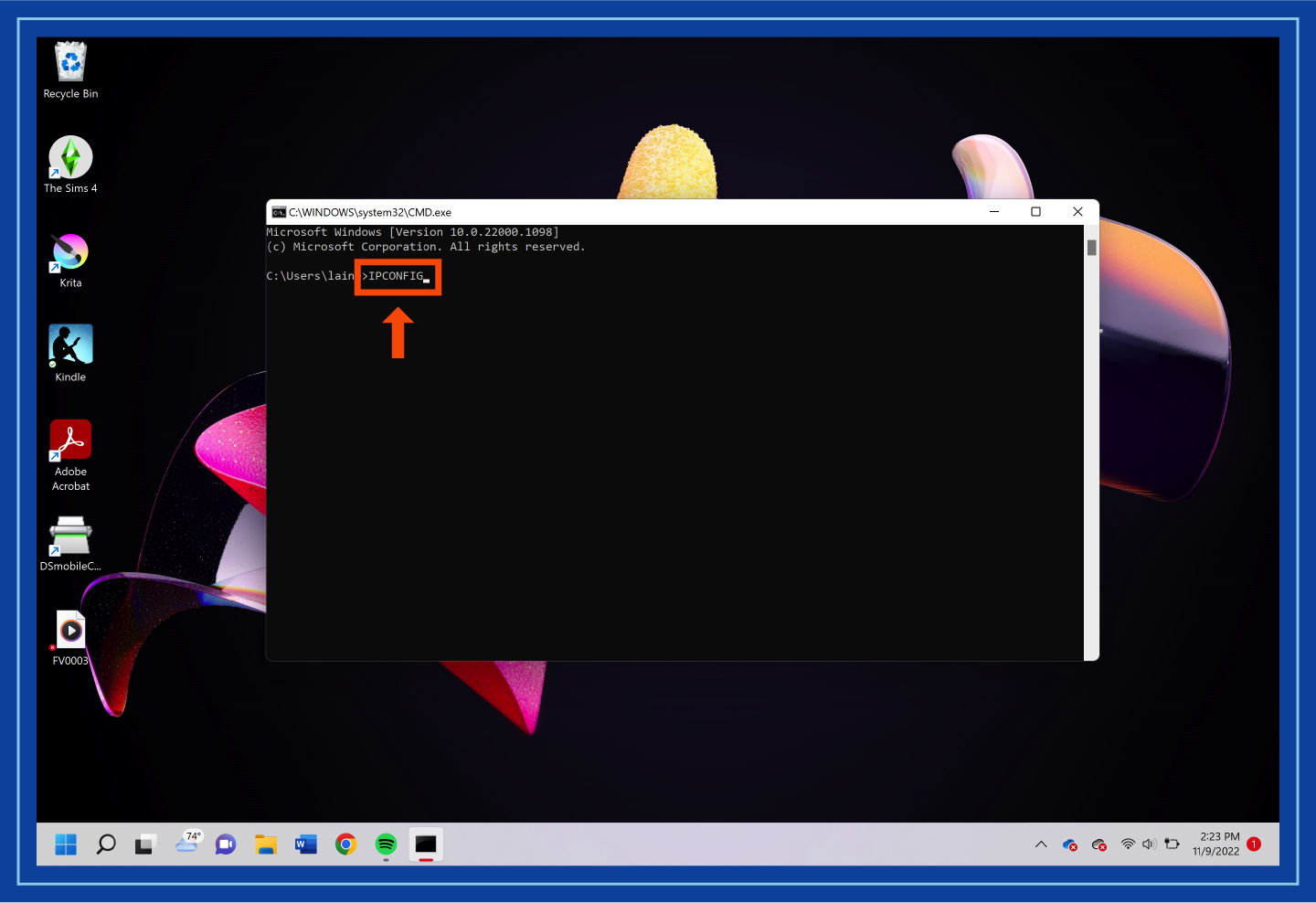
To find your IP address on Windows:
1. Open the Windows Command Prompt. This can be found in the Start menu.

2. Press Win + R.
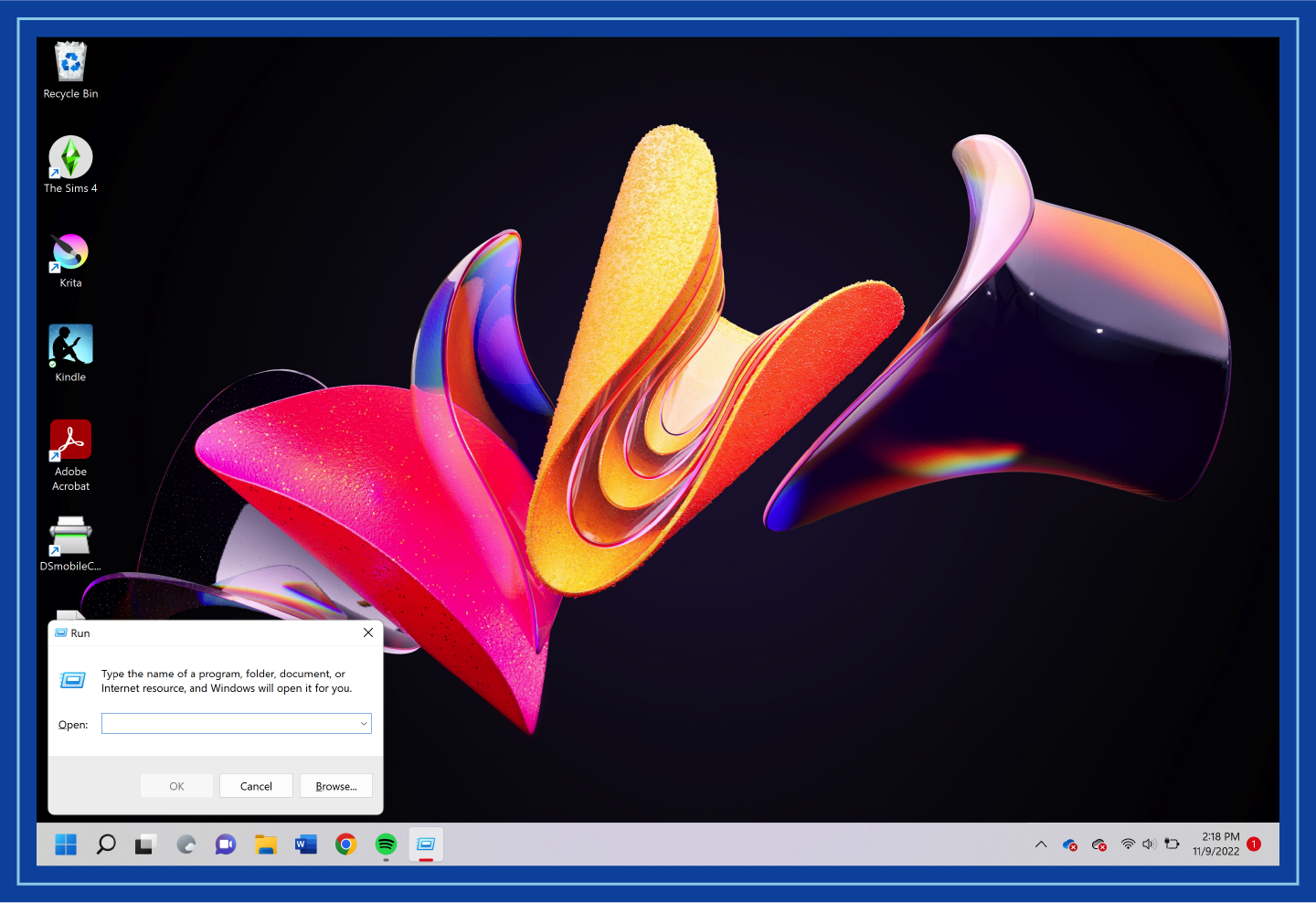
3. Type “cmd” and hit enter. A pop-up screen will appear.
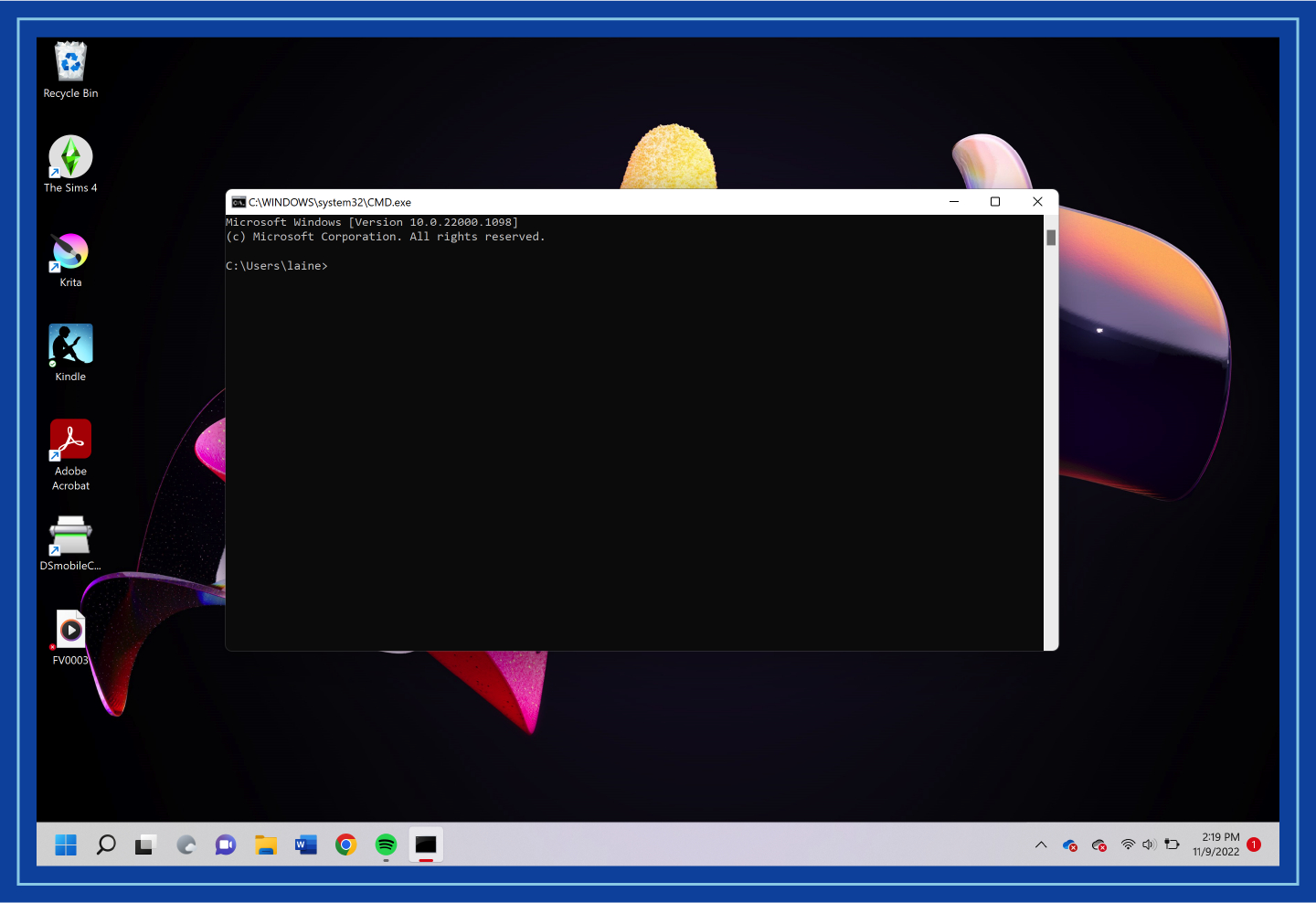
4. Enter “ipconfig” into the pop-up. Your private IP address should be displayed on the next screen.
To find your IP address on a Mac:
1. Open System Preferences.
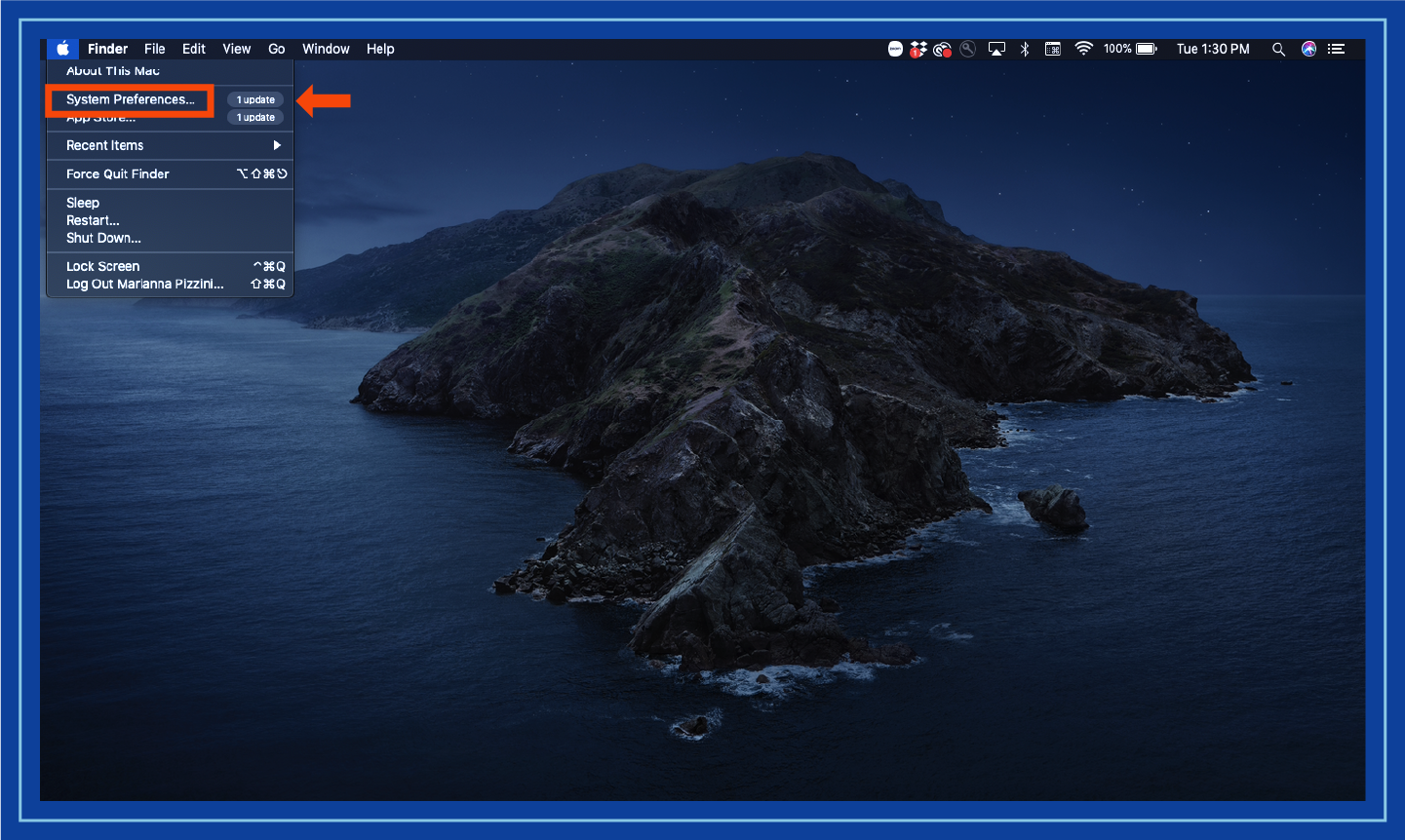
2. Select Network. Your private IP address should be displayed here.

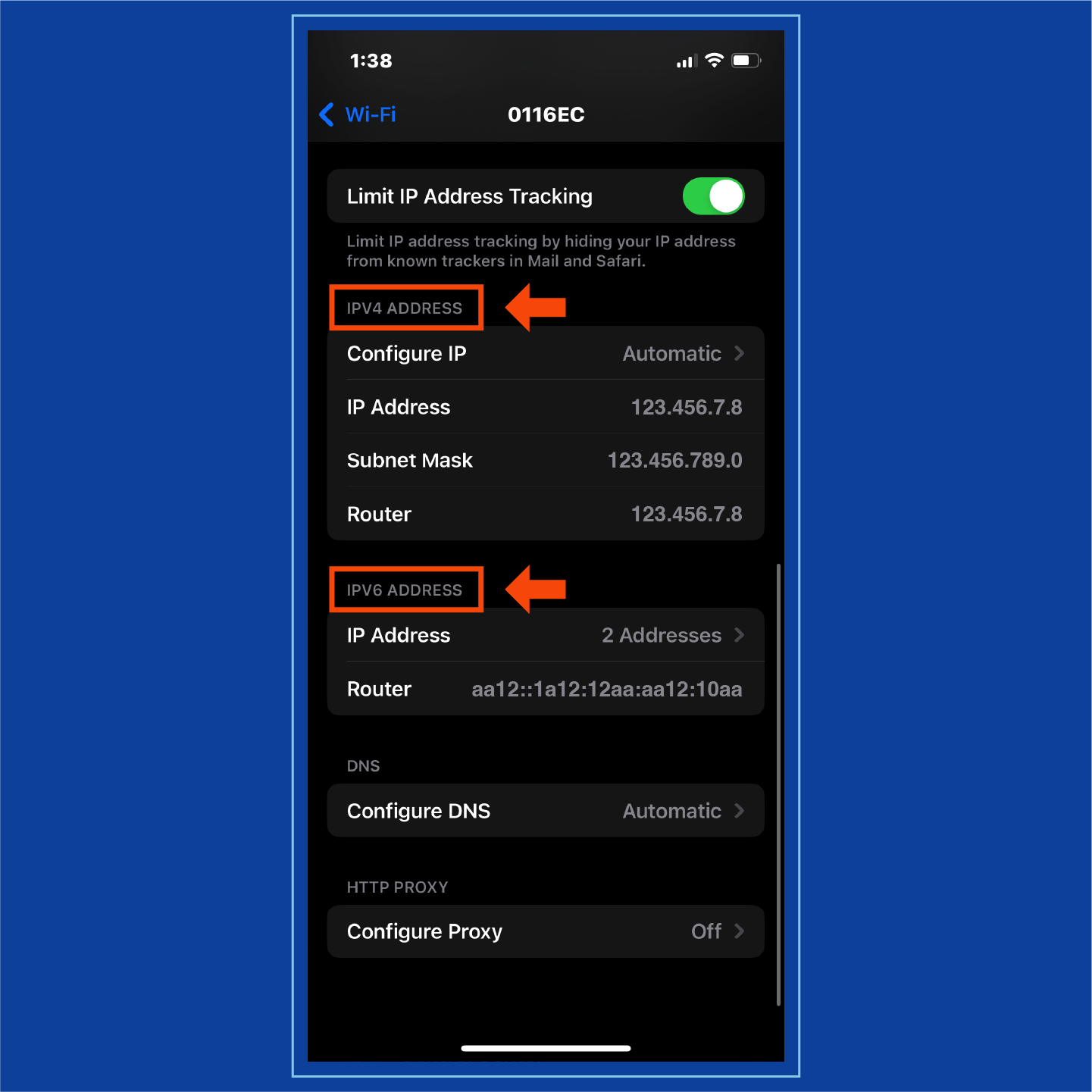
To find your IP address on an iPhone:
1. Open Settings.
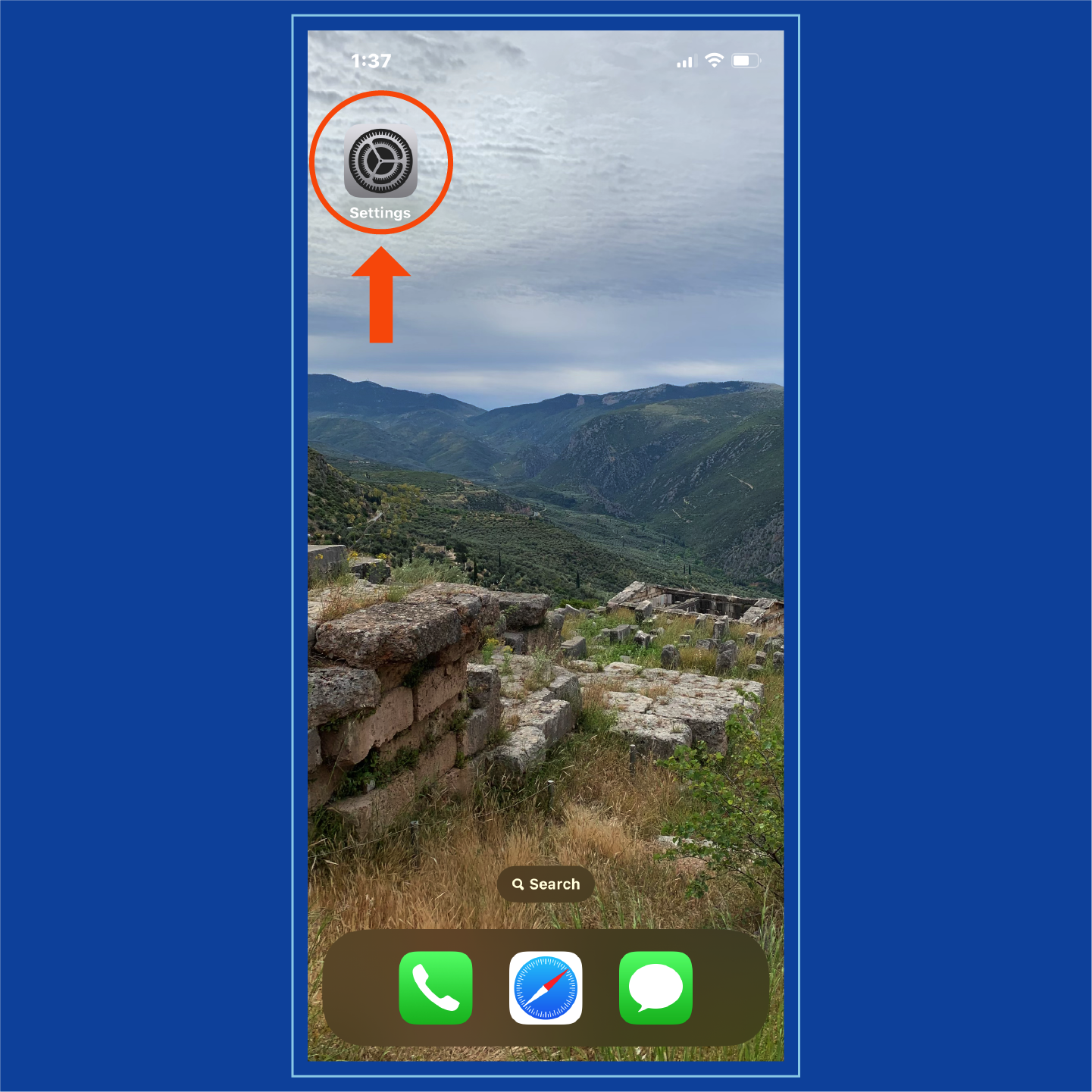
2. Select Wi-Fi.
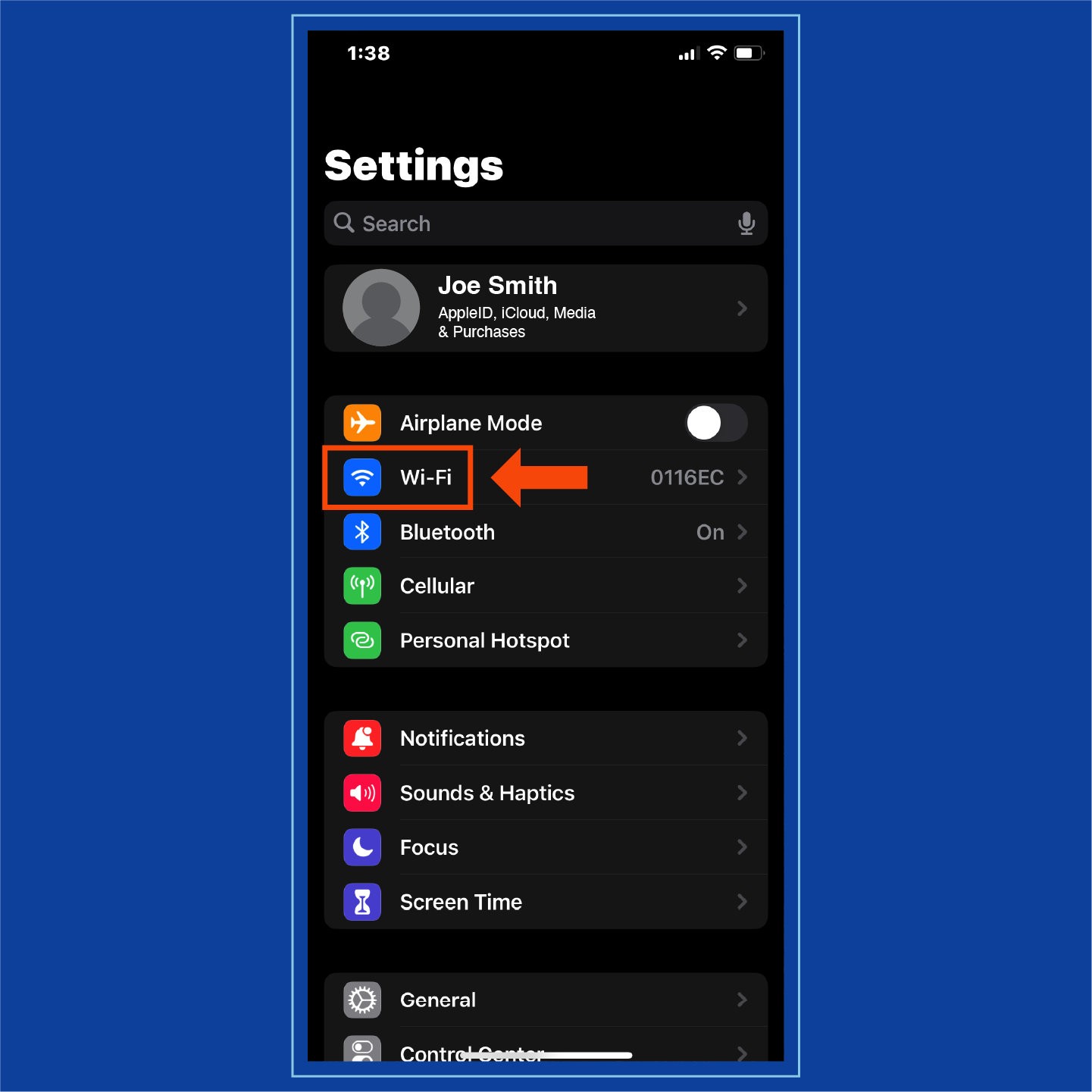
3. Navigate to your connected Wi-Fi information. This can be accessed by tapping the “i” next to your network name.
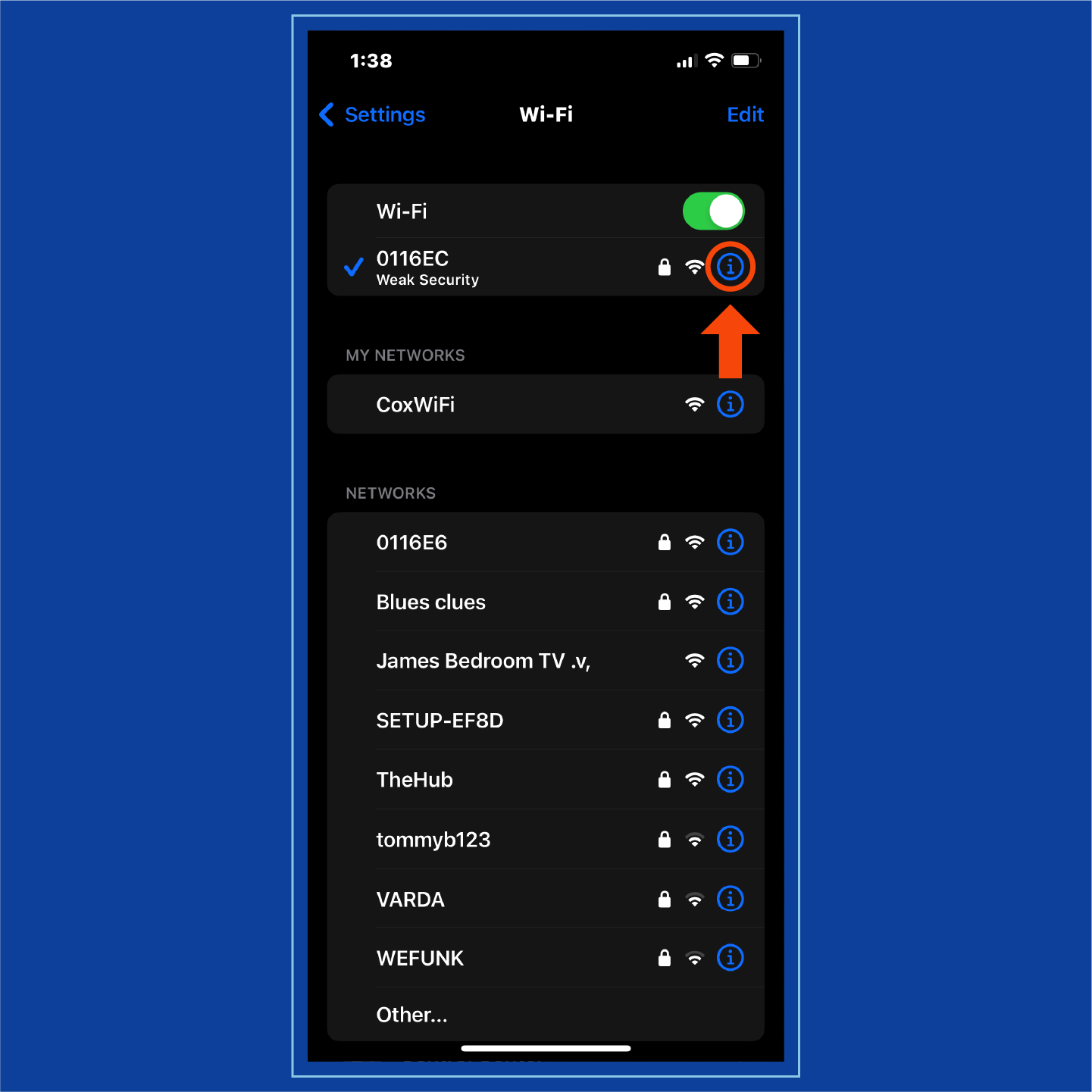
4. Find IPv4 and IPv6 sections. Your IP address can be found under these categories.
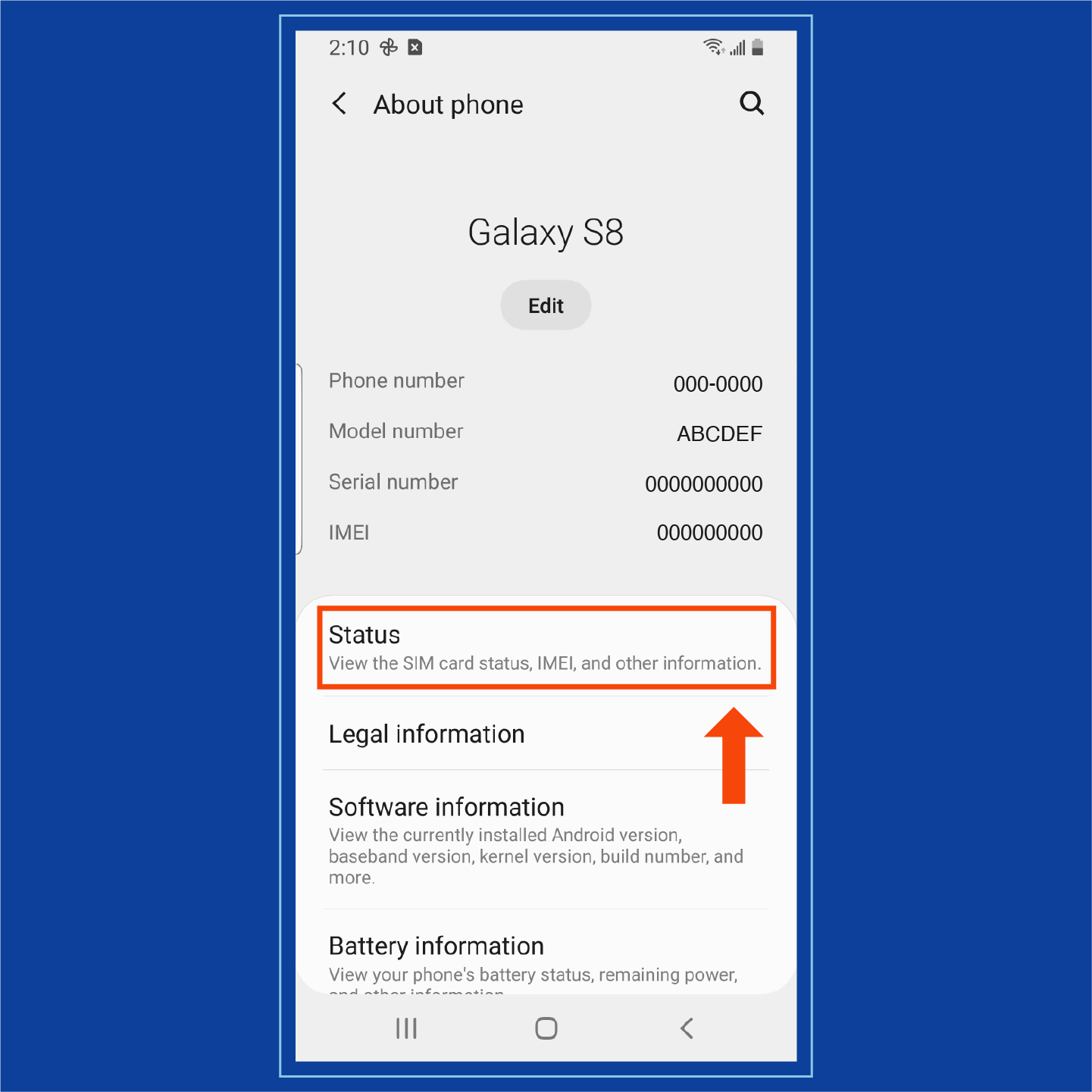
To find your IP address on an Android:
1. Open Settings.

2. Select About Phone.
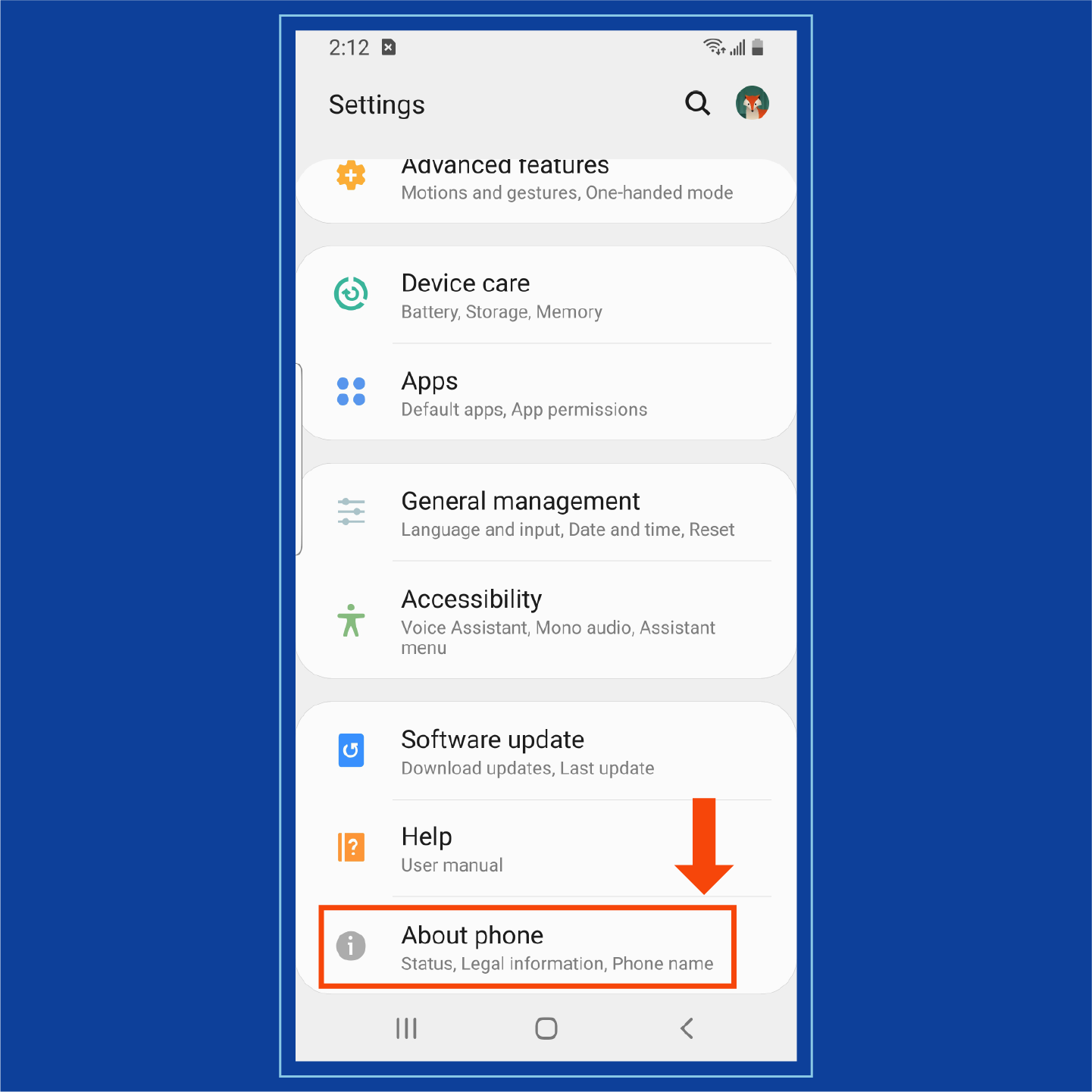
3. Choose Status. Your IP address should be clearly labeled and displayed here.
Your digital footprint can also lead others to your IP address. Some individuals who may try to find your address include:
- Authorities
- Hackers and cybercriminals
- Employers
- Advertisers
- Retailers
These individuals may try to find and use your IP address if you’re involved in illegal activity, have information they want to steal or they need a scapegoat for their own activities. If you believe your IP address has been compromised by malware or is being tracked, contact your ISP to reassign your identifier.
Who’s Interested in IP Addresses?
Your IP address may be of interest to other people, including:| Authorities | Authorities may track online activities, find geolocations for criminals or prove illegal activities. |
|---|---|
| Hackers and cybercriminals | Hackers may send personalized spam, spread malware across your network or spoof your address for their own activities. |
| Employers | Employers may track how you spend company time. |
| Advertisers | Advertisers may send you targeted ads or relevant products and services based on your online activities. |
| Retailers | Retailers may use your IP address to find your geolocation and determine the validity of your mailing address. |
Security Threats to IP Addresses
There are a variety of people who may need or want to know your IP address, and although it can be difficult to find, it isn’t impossible. If your IP address is found by hackers or other cybercriminals, you face possible security threats and dangers:
- Online stalking: In order for a cybercriminal to access your IP address, they need to stalk your online activity. If this occurs, they can eventually track down your location or even impersonate you across networks.
- Illegal downloads: Hackers will use IP addresses to download illegal content like pirated movies or trafficking images that can then be traced back to you.
- Location tracking: Anyone who knows your IP address can find your geolocation. This allows a hacker to know your region, state, city and sometimes ZIP or area code.
- Network attacks: An infected IP address is perfect for launching network attacks. These attacks — including DDoS attacks — use malware to shut down or overrun systems.
- Device hacking: IP addresses use ports to connect to devices. Hackers can use these ports to infiltrate devices where your personal information is stored — like mobile phones and computers.
Ways to Protect an IP Address
Although the security threats surrounding a hacked IP address are dangerous, there are still plenty of ways to protect your identifiers.
VPN
Using a VPN is one of the best and simplest ways to protect your IP address. VPNs use encryption to hide your online activity, so anyone trying to access your IP address should be unable to find it. Additionally, many VPNs may even change your geolocation as an added layer of security.
You should use a VPN when you:
- Use public Wi-Fi
- Travel
- Work remotely
- Want additional privacy
VPNs can be downloaded for free, and millions of people trust Panda Security downloads to protect their internet habits.
Proxy Server
Proxy servers are an additional security measure that can protect your personal IP addresses. These servers act as the middleman between a server or network and your device. However, it’s important to be aware that proxy servers can still track your online activities or insert ads into your online experience.
A proxy server works by first receiving and then rerouting any outside network or device communication to your device. If a hacker or cybercriminal attempts to access your IP address, they will find the identifier for your proxy server instead of your public or private IP address.
Antivirus Software
Although not a direct protection of your IP address, installing antivirus software can keep you aware of any suspicious network activity. An antivirus can alert you to possible hackers or device viruses, as well as keeping any information — including messages utilizing your IP address — encrypted.
Unique Passwords
Accessing your private IP addresses is quite simple if a hacker has access to your device, so varying your passwords and keeping them unique across your network can help protect your identifiers. If you use the same or similar passwords for a variety of devices or accounts, consider using a password generator to create distinct passwords for each.

IP addresses help identify devices across networks and are necessary for any type of device-to-device communication. While you may not be asking “What is an IP address?” anymore, you may be concerned about the security of your identification information. Protecting both private and public IP addresses with premium security defenses should be a priority.
Sources: Google Search Help | Guru99 | TP-Link | MUO