Phishing is a type of cyberattack in which cybercriminals use deceptive tactics to trick individuals into divulging sensitive information.
Some common types of phishing include:
- Smishing
- Email phishing
- Pharming
- Spear phishing
- Vishing
From deceptive emails and fake websites to social engineering tactics, there are numerous types of phishing attacks you can fall prey to.
By familiarizing yourself with the types of phishing attacks, you can better recognize and avoid falling victim to these scams, protecting your personal and sensitive information from getting into the wrong hands.
In this post, we’ll cover the different types of phishing attacks with examples and learn tips to prevent phishing attacks and stay secure in this ever-evolving digital landscape.

1. Email Phishing
Email phishing is a malicious technique cybercriminals use to trick individuals into revealing sensitive information or clicking on malicious links by impersonating legitimate entities via email. These deceptive emails often appear to be from trusted sources, such as government agencies or reputable companies.
These emails are often written with a sense of urgency, informing the recipient that a personal account has been compromised and they must respond immediately.
Their objective is to elicit a certain action from the victim, such as clicking a malicious link that leads to a fake login page. After entering their credentials, victims unfortunately deliver their personal information straight into the scammer’s hands.

Example of Email Phishing
You receive an email appearing to be from Gmail customer care that ends with “@Gm@il.com” requesting urgent action to update your account information due to a security breach. The email contains a link that redirects you to a fake website resembling the legitimate Gmail login page. Upon entering your credentials, the scammers capture your sensitive information for fraudulent purposes.
2. Spear Phishing
Spear phishing involves sending malicious emails to specific individuals within an organization. Rather than sending out mass emails to thousands of recipients, this method targets certain employees at specifically chosen companies. These types of emails are often more personalized in order to make the victim believe they have a relationship with the sender.
Example of Spear Phishing
A group called Star Blizzard, linked to the Russian FSB, is using spear-phishing attacks to target specific individuals and organizations, including government agencies and defense companies in the U.S. and the U.K. They trick people into revealing sensitive information by sending deceptive emails.
The U.S. National Security Agency and the U.K.’s NCSC have issued a warning to raise awareness and provide guidelines on how to protect against these attacks. Some of the recommended measures include using strong passwords, enabling multi-factor authentication, updating network and device security, being cautious of suspicious emails and links and using email scanning features to detect phishing attempts.
3. Whaling
Whaling is a type of cyberattack that targets high-profile individuals or executives within an organization, often referred to as “whales” due to their significance within the company. Unlike traditional phishing attacks that cast a wide net to lure in victims, whaling attacks are highly targeted and personalized.
This includes the CEO, CFO or any high-level executive with access to more sensitive data than lower-level employees.
Oftentimes, these emails use a high-pressure situation to hook their victims, such as relaying a statement of the company being sued. This entices recipients to click the malicious link or attachment for more information.
Example of Whaling
The CEO of a large corporation receives an urgent email from what appears to be the CFO, requesting sensitive financial information for an upcoming merger. Believing it’s a legitimate request from a trusted colleague, the CEO provides the information. However, the email was a whaling attack orchestrated by a cybercriminal who impersonated the CFO to gain access to sensitive company data.
4. Smishing
SMS phishing, or smishing, leverages text messages rather than email to carry out a phishing attack. They operate much in the same way as email-based phishing attacks: Attackers send texts from what seem to be legitimate sources (like trusted businesses) that contain malicious links. Links might be disguised as a coupon code (20% off your next order!) or an offer for a chance to win something like concert tickets.
Example of Smishing
Researchers discovered a new phishing tool called SNS Sender, which uses Amazon Web Services to send scam texts pretending to be from USPS about failed deliveries. The suspected author of SNS Sender is known by the alias “ARDUINO_DAS.”
The SNS Sender tool inserts links to fake USPS websites that collect victims’ personal information, like names, addresses, phone numbers, emails and credit card numbers. This technique of using cloud services for phishing attacks is a new and previously unseen method.
5. Vishing
Vishing, short for “voice phishing,” is a type of catphishing cyberattack where fraudsters use phone calls to deceive individuals into providing sensitive information or performing certain actions.
In a vishing attack, scammers pretend to contact on behalf of a bank, government agencies or tech support, using social engineering tactics to manipulate victims into disclosing personal or financial information, such as account numbers, passwords or verification codes. These attacks often exploit fear or urgency to pressure victims into compliance and can result in identity theft, financial loss or unauthorized access to sensitive accounts.
Example of Vishing
You receive a phone call from a person claiming to be a representative from your bank’s fraud department. They inform you of suspicious activity on your account and advise you to provide your account details to verify your identity and prevent any fraudulent transactions.
Believing it to be a legitimate call, you comply and provide the requested information. However, the call was a vishing attack, and the caller was a cybercriminal who now has access to your sensitive financial data.
6. Business Email Compromise (CEO Fraud)
Business email compromise (BEC), also known as CEO fraud or email account compromise, is a form of phishing in which the attacker obtains access to the business email account of a high-ranking executive (like the CEO).
With the compromised account at their disposal, they send emails to employees within the organization impersonating the CEO to initiate a fraudulent wire transfer or obtain money through fake invoices.

Example of CEO Fraud
A finance department employee receives an email appearing to be from the CEO, requesting an urgent wire transfer to a vendor. Believing it’s legitimate, the employee initiates the transfer, but the email was part of a BEC attack. Cybercriminals had compromised the CEO’s email account, resulting in a significant financial loss for the company.
7. Clone Phishing
Clone phishing works by creating a malicious replica of a recent message you’ve received and re-sending it from a seemingly credible source. Any links or attachments from the original email are replaced with malicious ones. Attackers typically use the excuse of resending the message due to issues with the links or attachments in the previous email.
Examples of Clone Phishing
Phishing scammers created fake websites that look like popular crypto media outlets Blockworks and Etherscan. They tricked people into connecting their crypto wallets by posting fake news about a supposed Uniswap exploit on Reddit. The fake Etherscan website had a tool claiming to check for approvals but instead drained wallets.
The scammers hoped to steal at least 0.1 Ether (worth $180), but their setup didn’t work as planned. The fake websites were registered on October 25, 2023, and similar scams were seen on other crypto news sites like Decrypt.
8. Evil Twin Phishing
Evil twin phishing involves setting up what appears to be a legitimate Wi-Fi network that lures victims to a phishing site when they connect to it. Once they land on the site, they’re typically prompted to enter their personal data, such as login credentials, which then goes straight to the hacker. Once the hacker has these details, they can log into the network, take control of it, monitor unencrypted traffic and find ways to steal sensitive information and data.
Example of Evil Twin Phishing
You connect to what you believe is a cafe’s free Wi-Fi network, but it’s a rogue hotspot set up by cybercriminals, known as an “evil twin.” They intercept your online activity, including logging into your email account. Later, you receive a phishing email pretending to be from your email provider, prompting you to log in to verify your identity. Unknowingly, you enter your credentials on a fake website created by cybercriminals, giving them access to your email account.
9. Social Media Phishing
Social media phishing is when attackers use social networking sites like Facebook, Twitter and Instagram to obtain victims’ sensitive data or lure them into clicking on malicious links. Hackers may create fake accounts impersonating someone the victim knows to lead them into their trap, or they may even impersonate a well-known brand’s customer service account to prey on victims who reach out to the brand for support.

Example of Social Media Phishing
You receive a direct message on social media from a fake account that appears to be a friend or acquaintance asking you to click on a link to watch a video or view a photo. Without suspicion, you click the link, which leads you to a fake login page designed to steal your social media credentials. You enter your username and password, handing them over to cybercriminals who can now access your account and potentially exploit it for malicious purposes.
10. Search Engine Phishing
Search engine phishing involves hackers creating websites and getting them indexed on legitimate search engines. These websites often feature cheap products and incredible deals to lure unsuspecting online shoppers who see the website on a Google search result page.
If they click on it, they’re usually prompted to register an account or enter their bank account information to complete a purchase. Of course, scammers then turn around and steal this personal data to be used for financial gain or identity theft. To stay safe — make sure you’re using a secure search engine for all your online activities.
Example of Search Engine Phishing
You search for a popular website, such as Amazon.com, on a search engine and click on one of the top results. However, instead of being directed to the legitimate website, you’re taken to a convincing but fake version (something like Am@zon.com) designed to mimic the original site.
Unaware of the deception, you enter your login credentials or sensitive information, thinking it’s an authentic site. In reality, you’ve fallen victim to search engine phishing.
11. Pharming
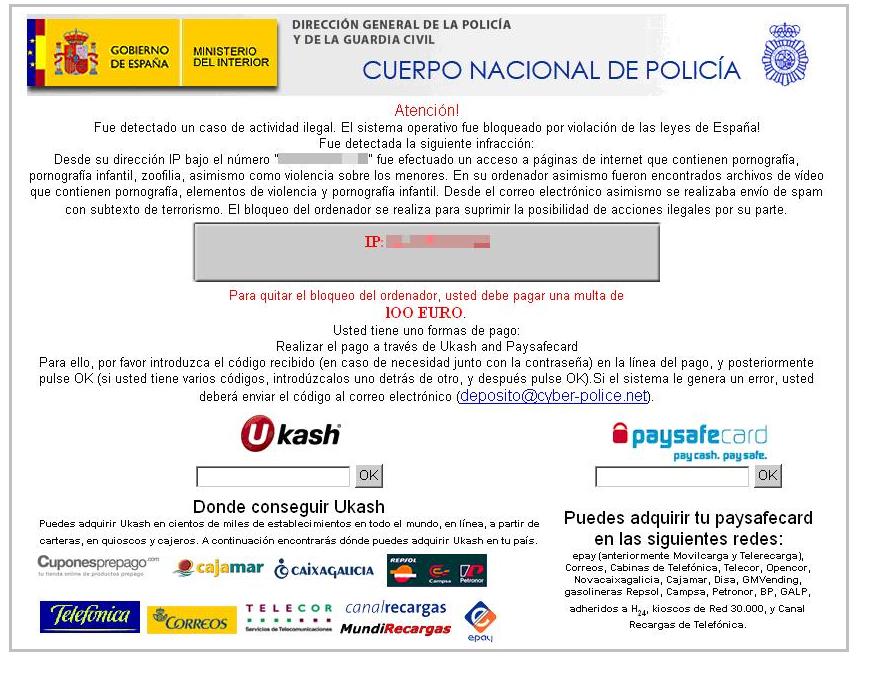
Pharming — a combination of the words “phishing” and “farming” — involves hackers exploiting the mechanics of internet browsing to redirect users to malicious websites, often by targeting Domain Name System (DNS) servers. DNS servers exist to direct website requests to the correct IP address.
Hackers who engage in pharming often target DNS servers to redirect victims to fraudulent websites with fake IP addresses. Victims’ personal data becomes vulnerable to theft by the hacker when they land on the website with a corrupted DNS server.
Example of Pharming
You type in the URL of your bank’s website into your web browser and hit enter. However, instead of being directed to the legitimate bank website, you’re redirected to a fake website that looks identical to the real one.
Unbeknownst to you, your computer has been compromised by malware or your DNS settings have been tampered with, redirecting you to a fraudulent website controlled by cybercriminals. Thinking it’s the real site, you proceed to enter your login credentials and other sensitive information, unknowingly handing them over to the attackers.
Tips to Spot and Prevent Phishing Attacks
One of the best ways you can protect yourself from falling victim to a phishing attack is by studying examples of phishing in action. This guide by the Federal Trade Commission (FTC) is useful for understanding what to look for when trying to spot a phishing attack, as well as steps you can take to report an attack to the FTC and mitigate future data breaches. In general, keep these warning signs in mind to uncover a potential phishing attack:
- An email asks you to confirm personal information: If you get an email that seems authentic but seems out of the blue, it’s a strong sign that it’s an untrustworthy source.
- Poor grammar: Misspelled words, poor grammar or a strange turn of phrase is an immediate red flag of a phishing attempt.
- Messages about a high-pressure situation: If a message seems like it was designed to make you panic and take action immediately, tread carefully — this is a common maneuver among cybercriminals.
- Suspicious links or attachments: If you received an unexpected message asking you to open an unknown attachment, never do so unless you’re fully certain the sender is a legitimate contact.
- Too-good-to-be-true offers: If you’re contacted about what appears to be a once-in-a-lifetime deal, it’s probably fake.
Tips to Prevent Phishing Attacks
Let’s look at some tips to help you protect yourself from deceptive phishing attempts.
- Be skeptical of unsolicited emails: Avoid clicking on links or downloading attachments in emails from unknown or unexpected sources. Verify the legitimacy of the email by contacting the sender through a trusted and official communication channel.
- Check URLs carefully: Hover over links to preview the actual URL before clicking. Ensure the website’s address matches the expected domain, especially when prompted to enter sensitive information.
- Use multi-factor authentication (MFA): Enable MFA whenever possible, as it boosts account security even if your credentials are compromised.
- Keep software and systems updated: Update your system applications and antivirus software to patch vulnerabilities that attackers may exploit.
- Educate and train: Make sure you and your family follow cybersecurity best practices. Encourage open communication with kids and make them aware of data privacy best practices.
The next best line of defense against all types of phishing attacks and cyberattacks in general is to make sure you’re equipped with a reliable antivirus. At the very least, take advantage of free antivirus software to better protect yourself from online criminals and keep your personal data secure.