Venezuela recently suffered a series of blackouts that left 11 states without electricity. From the outset, Nicolás Maduro’s government claimed that it was an act of sabotage, made possible with electromagnetic attacks and cyberattacks on the National Electric Corporation (Corpoelec) and its power stations. By contrast, Juan Guaidó’s government simply put it down to the “the inefficiency [and] the incapability of the regime.”
Without an impartial and detailed diagnosis, it is difficult to establish whether the real cause of the blackouts was sabotage or simply lack of maintenance. Nevertheless, the allegations of supposed sabotage poses some interesting questions about cybersecurity. Many control systems in critical infrastructures such as power stations are closed and don’t have external Internet connections. It’s therefore worth asking: could a cyberattacker access closed IT systems without direct contact with the computers? The answer is yes. Electromagnetic waves could be an attack vector.
How to capture electromagnetic emanations
All electronic devices emit radiation and emanations in the form of electromagnetic and acoustic signals Depending of several factors, such as distance and obstacles, eavesdroppers can capture signals from components via antennae or highly sensitive microphones (in the case of acoustic signals) and process them in order to obtain information. These devices include monitors and keyboards, and as such, these techniques can also be employed by cyberattackers.
In the case of monitors, in 1985, the researcher Wim van Eck published the first unclassified document about the security risks that emanations from these devices pose. Back then, monitors used Cathode-ray tubes (CRT). His research demonstrated that radiation from a monitor can be captured at a distance and that this radiation can be used to show the images on the monitor. It is known as van Eck phreaking and, in fact, it is one of the reasons that several countries, including Brazil and Canada, have deemed electronic voting systems to be too unsafe to use.
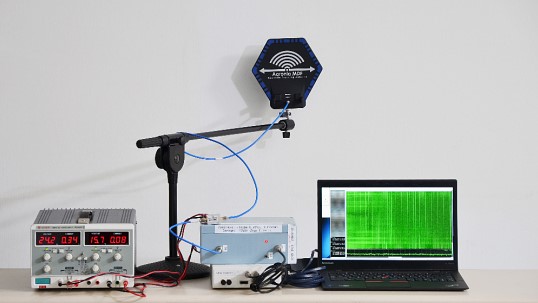
Although LCD monitors these days emit less radiation than CRT, recent research has shown that they too are vulnerable. What’s more, a team from Tel Aviv University demonstrated this in a study. They managed to gain access to encrypted content on a laptop in an adjacent room using a simple $3,000 piece of equipment made up of an antenna, an amplifier, and a laptop with software to process the signals.
On the other hand, keyboards themselves can also be sensitive to their emanations being intercepted. This means that there is a potential risk of cyberattackers figuring out credentials and passwords by analyzing which keys are pressed.
TEMPEST and EMSEC
The use of emanations to obtain information began during the First World War, in telephone wires. It was used heavily during the Cold War with more advanced devices. For example, a declassified NASA document from 1973 explains how, in 1962, a member of the security detail in the US Embassy in Japan discovered that a dipole in a nearby hospital was pointed at the building in order to capture its signals.
But the concept of TEMPEST as such begins to appear in the 70s, with the first security directives about emanations that appeared in the USA. It is a code name that refers to research and studies about unintentional emanations from electronic devices that can leak classified information. TEMPEST was created by the US National Security Agency (NSA) and resulted in a series of security specifications that were also adopted by NATO.
It is very often used interchangeably with the term EMSEC (emissions security), which is a specific subset of COMSEC (communications security).
TEMPEST protection
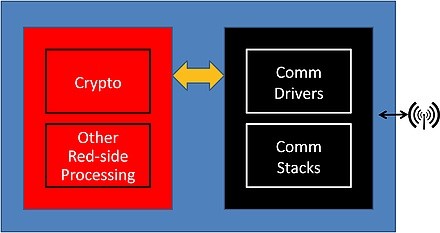
Firstly, TEMPEST protection is applied to a basic concept of cryptography known as Red/Black architecture. This concept separates systems into those that contain or transmit plaintext – i.e., unencrypted – sensitive information (Red) and those that emit encrypted messages (Black). One of the premises of TEMPEST protection is this separation that segregates all the components.
Secondly, it is important to bear in mind the fact that all devices emit a certain level of radiation. This means that the highest possible level of protection would be to completely shield the entire space, as well as computers, systems and components. However, this would be extremely costly and impractical for most organizations. For this reason, more partial techniques, such as the following, are used.
- Zoning evaluation: This is used to examine the level of TEMPEST security of spaces, installations, and computers. Once this evaluation has been carried out, resources can be directed to those components and computers that contain the most sensitive information, or unencrypted data (Red). Different official communications security bodies, such as the NSA in the US, or the CCN in Spain, certify these evaluations.
- Shielded areas: a zoning evaluation may determine that certain spaces that contain computers don’t fulfill security requirements. In these cases, one option is to completely shield a space, or to use shielded cupboards for any computers. These cupboards are made of special materials that stop emanations.
- Computers with their own TEMPEST certifications: at times, it is possible for a computer to be in a secure location but still lack adequate security. To reinforce the existing security, there are computers and communications systems that have their own TEMPEST certification, which certifies that their hardware and other components are secure.
TEMPEST shows that, even if an organization’s systems don’t leave apparently secure physical spaces, or aren’t even connected, they are not necessarily totally safe. In any case, most vulnerabilities in critical infrastructures are due to more conventional attacks, such as ransomware, as we recently pointed out. In these cases, such attacks can be avoided more simply, with appropriate measures and advanced cybersecurity solutions. The combination of all these security measures is the only way to guarantee the safety of the systems critical to the future of an organization, or even a country.