366 posts
How to avoid disaster in the event of credit card theft
When it comes to choosing PINs for your credit card and cellphone you’ve done everything right – you avoided the temptation to use the year…
How to get the best out of your computer
You have surely, at one point or another, missed the speed at which your computer once worked when it was new. Now, when you turn…
10 easy-to-follow online safety tips for grandparents
Online security has no age limits and we can all protect ourselves from cybercriminals without being experts in the field. All you need to do…
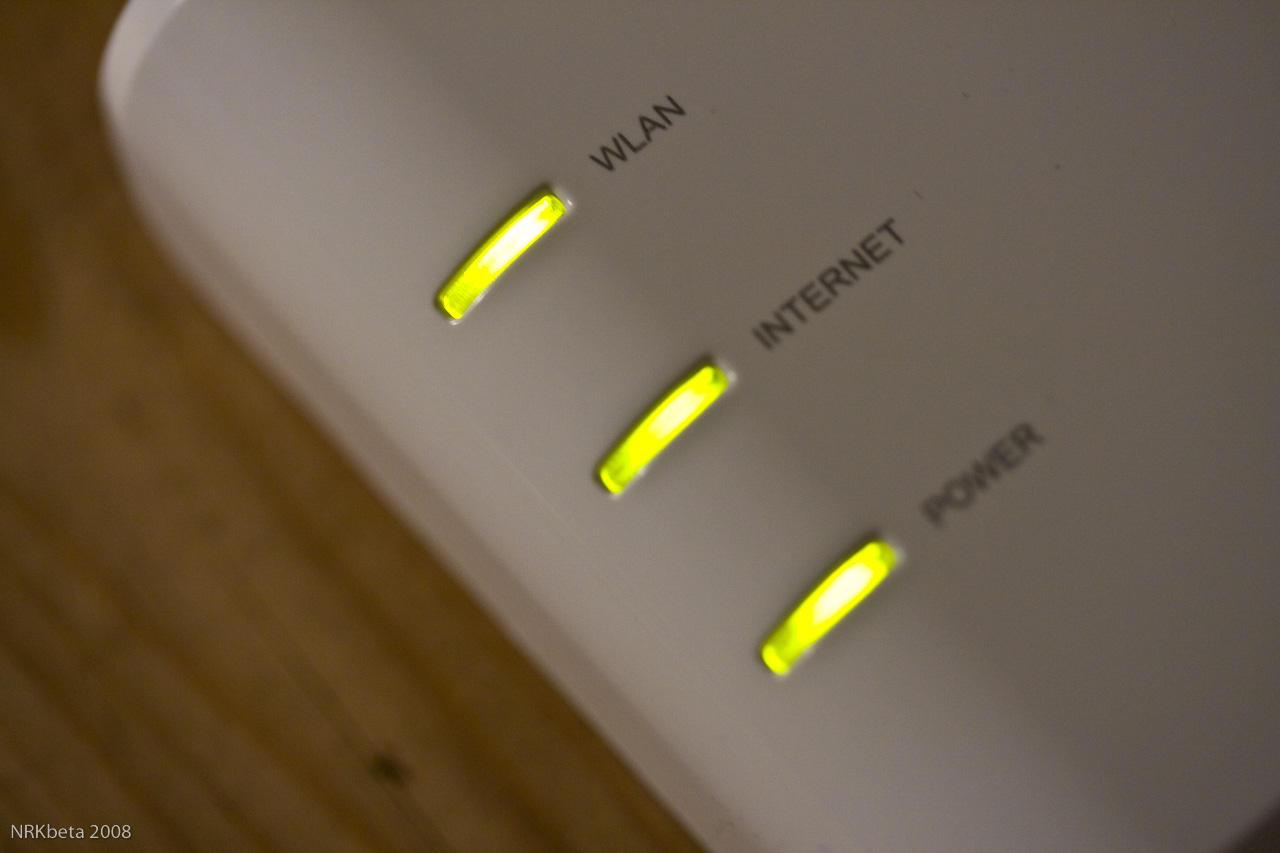
How to set up your household router to protect yourself from attack
To keep your electronic devices secure, it isn’t just important to be aware of cyberattacks that could arrive via emails or false links. You need…
How to protect your company from Zero-Day attacks
Any attack that takes advantage of the “window of opportunity” produced by recently discovered vulnerabilities is called a Zero-Day attack. In other words, a rapid…
Keeping tabs on your employees in a multi-device environment
The traditional desktop computer is no longer the only device we use to get work done. For the past few years workers have increasingly begun…
5 security measures that experts follow (and so should you!)
When you’re watching a movie and you see the typical computer screen filled with green coding (you know the type, rows of 1s and 0s)…