Neither personal information nor fingerprints have been safe from cybercriminals in the past year and, as the year comes to a close, one thing is for sure – the more devices that we have, the more security we need.
Throughout the course of the year, cybercriminals have shown that they are capable of discovering and, taking advantage of, any vulnerability possible in order to get their hands on our data or to control our devices. Below is a roundup of the most damaging and alarming of these attacks.
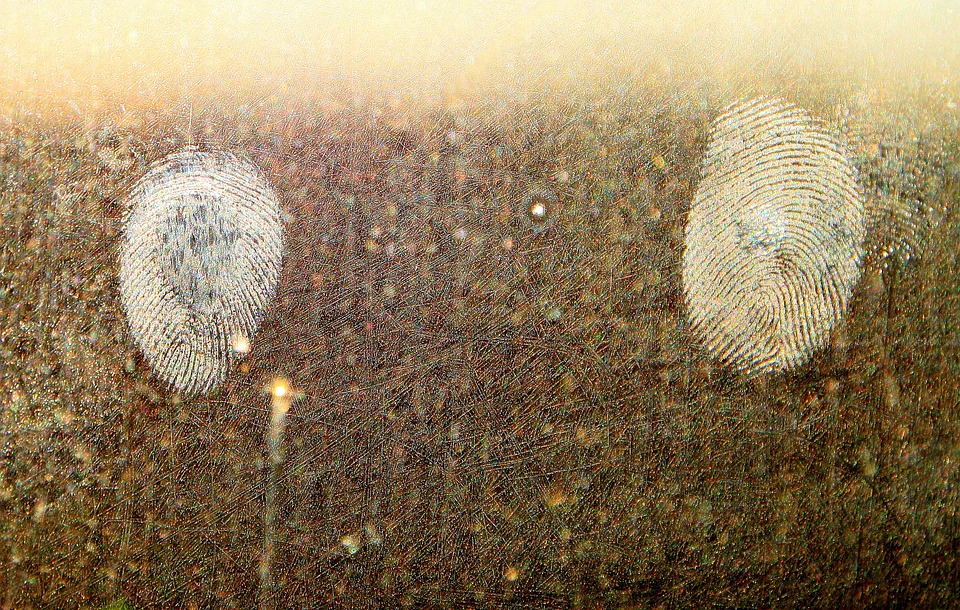
Fingerprint theft
If fingerprints are seen as one of the most secure methods of biometric security (they are the current method of unblocking iPhones), the theft of information belonging to US government employees showed that there are serious things to consider with the system.
Last June, a group of cybercriminals managed to obtain the fingerprints of nearly six million federal workers, which could put not only their mobile phones in danger, but even the security of the country.
Remote control of smart cars
Another of the big challenges facing cybersecurity is the issue of smart cars. Until there is a solution, these cars will continue to be vulnerable to manipulation. Last summer, two hackers showed that it was possible to take advantage of errors in the computer system onboard a Jeep Cherokee and took control of the car, even managing to apply the brakes on the vehicle, all carried out remotely.
Thousands of compromised Android devices
Not all of the vulnerabilities in the world of IT security are focused on modern tools or devices. In fact, smartphones have been at the center of a massive scandal in 2015, when thousands of Android devices were affected by Stagefright, a security failure which allowed cybercriminals to access any Android phone and control it without the owner knowing.
The online dating furor
Without a doubt the biggest scandal of the year was the leaking of information relating to more than 32 million users of the online dating site Ashley Madison. This sent shockwaves through the cybersecurity world and served to remind everyone, both platforms and users, of the dangers facing IT security.
A vulnerable infusion pump
The health and safety of people is also at risk due to the vulnerabilities of different devices. It’s not just smart cars that can be manipulated and involved in accidents, as this year an infusion pump used in hospitals to administer patients’ medicine had to be removed. It turned out that if a cybercriminal had connected to the hospitals’ networks, they could have accessed the machine, manipulating it and changing its settings.
Gas stations at risk
It’s not just hospital pumps that are in danger, as investigations carried out on both sides of the Atlantic uncovered the risks facing gas stations. Once connected to a network, these pumps could be attacked, and a cybercriminal could even cause one to explode.
A year to forget for Apple
2015 has been the worst year for Apple in terms of security as the number of attacks directed at its devices has increased five-fold on the previous year, while the number of new vulnerabilities has continued to grow. One such example is the bug Dyld, which was discovered over the summer and affected the MAC OS X operating system.
Data stolen via third-parties
15 million T-Mobile customers had their data stolen by cybercriminals this year. According to the company, the information wasn’t taken from their own servers, but rather stolen from the company that looked after payments for T-Mobile’s customers.
Data theft via web browsers
The biggest names in the technology sector haven’t escaped the year without a few scares. Last summer Firefox had to advise its users that a failure in the browser meant that cybercriminals could have looked for and stolen files without the victim realizing.
A bad end to the year for Dell
The final scandal of the year happened last month, when it was discovered that the latest models of Dell computers were hiding a serious security failure. Thanks to this vulnerability, cybercriminals were able to alter the communication between various different systems and steal information from the affected computers.