Data kidnapping is exactly as it sounds — dangerous, scary and run by cyberthieves looking to rake in a profit when you pay their ransom. Plus, you don’t need to be a millionaire or a successful corporation to be the target of a ransomware attack.
Because many people feel the risk of losing their data is too great, it’s all too common for victims to pay an attacker’s ransom. In fact, ransomware attacks have become so successful that ransom demands are increasing — and still being paid!
The best way to combat ransomware is by not becoming a victim in the first place. By following these 16 best practices and investing in premium protection services, you can keep yourself or your organization safe from ransomware attacks.
1. Protect Ports and Settings
Some variants of ransomware use open ports and their settings to remotely attack or block users. You or your organization can protect these ports by limiting connections to only trusted servers — both in the cloud and on an organization’s premises.
2. Download a VPN
Using the public internet without additional protection is one of the most common ways cyberthieves and hackers attack systems. By downloading a VPN, you can protect your IP address, personal information and transmitted data — even if you access a public network without a WPA2 key.
3. Install Antivirus Software
Ransomware is constantly evolving as hackers develop new, more dangerous strains. Unless you download and install comprehensive antivirus software, your data is still vulnerable to attack.
4. Secure Backup Files
If your data is irretrievable after an attack, you’re more likely to fall victim. Keep a backup copy of your files available in case your are threatened by a hacker. Plus, you can secure these files by keeping copies on both the cloud and a hard drive so their accessible with and without Wi-Fi, and a consistent backup schedule can help ensure that your files are up-to-date.
5. Set Up Configuration Settings
Don’t rely on your default configuration settings to protect your systems from ransomware attacks. Instead, make sure you reevaluate your secure configuration settings to close security gaps and minimize threats. Additionally, you may want to consider enabling firewalls as an additional layer of security.
6. Harden Endpoints
In addition to your configuration settings, you should invest in endpoint security. Many attackers will exploit endpoint vulnerabilities, but anti-tampering protocols and alerts can help protect information by hardening endpoints. It’s also important to design and develop a patch management protocol to keep systems updated with new and improved endpoint security reforms.
7. Apply Network Segmentation
Network segmentation refers to the division of networks within an organization or system. These segments usually contain workers or devices from the same divisions, and they are used to stop lateral threats.
For example, if an organization segments a data information system away from an organizational information system and one is compromised, the other should be able to maintain its individual security protocols and keep the threat at bay.
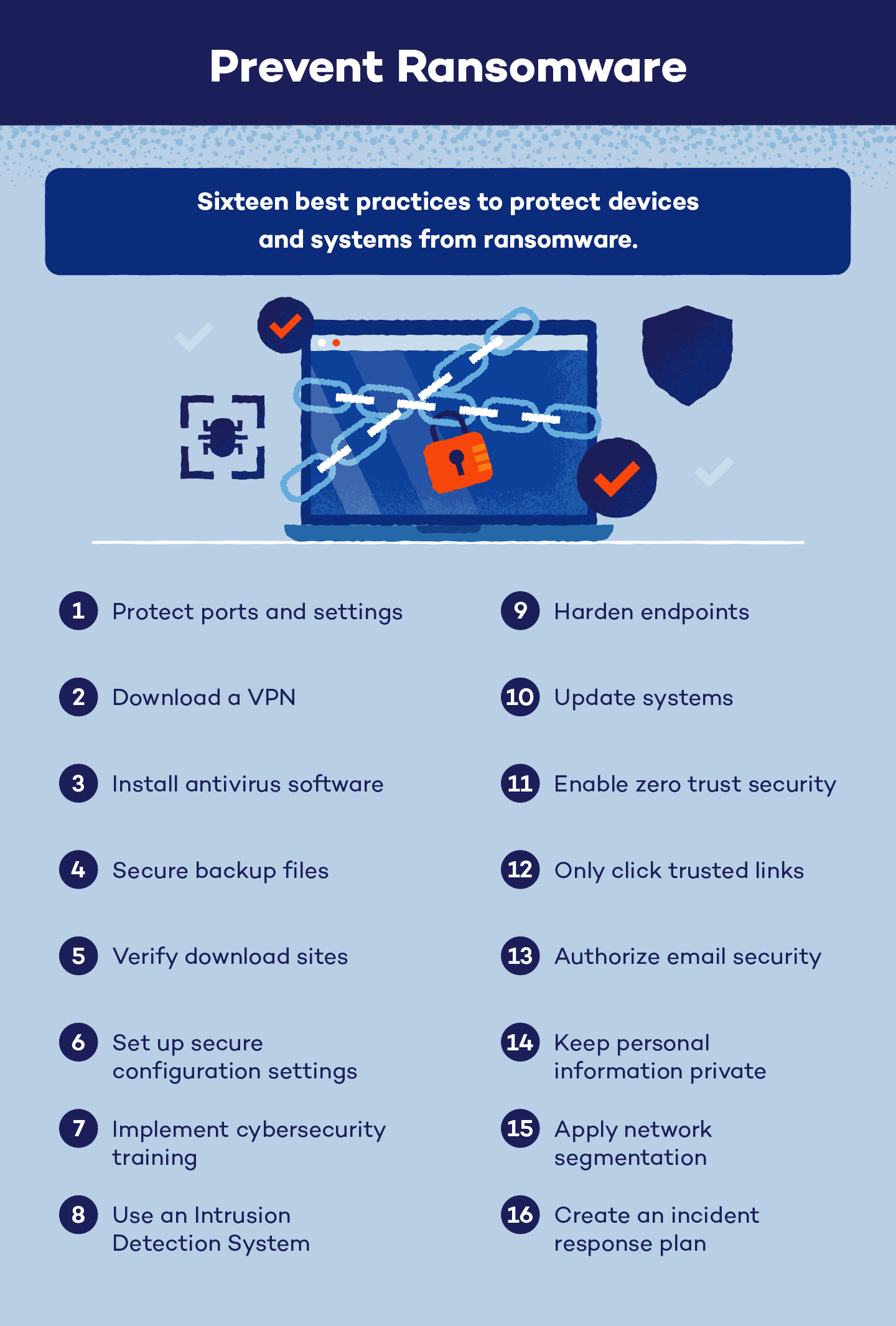
8. Update Systems
One of the major steps to preventing ransomware is to update your operating system (OS) consistently. If your OS isn’t up to date, you can’t take advantage of security updates, and cyberthieves can find and exploit holes that haven’t been patched by newly released system fixes.
9. Enable Zero Trust Security
A zero-trust security model assumes that everyone attempting to access a network is a threat until their identity is checked and verified. This includes both internal and external accessors. Users are required to use multi-factor authentication to access systems, and Network Access Control (NCA) is restricted to only authorized personnel and devices.
10. Verify Download Sites
If you’re downloading a PDF, an app or a document from an email, verify the sender or the download site. Many attackers will masquerade dangerous downloads as common, harmless apps or documents, so it’s important to check that you are downloading information from a reputable source.
11. Only Click Trusted Links
Similar to verifying download sites, only click links from trusted sources. Links from organizational management or other system workers should be verified, but any type of unidentified pop-up, email or miscellaneous message could contain malware and should not be clicked until identified.
12. Use an Intrusion Detection System
An Intrusion Detection System (IDS) searches through network activity, logins and signatures for any malicious activity. These systems keep detailed, updated records of a system’s frequent account activity in order to quickly identify anything out of the ordinary.
13. Keep Personal Information Private
If ransomware can’t be dumped on your system from infected downloads or encrypted messages, hackers may try to infiltrate your systems by using your personal information. Keep this data private — away from social media accounts and secured in data or password managers — to prevent ransomware from infecting your devices.
14. Authorize Email Security
Phishing scams can trick users into opening infected attachments, compromising an organization’s or system’s integrity. To prevent phishing and ransomware attacks, authorize and adjust your email security settings. Many programs can identify phishing emails based on their subject lines or sender emails and will automatically note them as spam or block their messages.
15. Implement Cybersecurity Training
Even if your systems are up-to-date and running effectively, you need to train your team and yourself about the dangers and signs of ransomware. These trainings should be updated regularly and be a mandatory component of onboarding for organizations.
16. Create an Incident Response Plan
Even if you’ve followed every best practice to prevent ransomware, it’s still possible for a successful attack to occur. To combat this reality, organizations should create and implement incident response plans and assign individuals specific tasks ahead of a ransomware attack. Additionally, these plans should be tested frequently and updated with new methodologies as ransomware strains evolve.
Best practices are the most effective ways to prevent ransomware. Even if your systems are compromised or have been in the past, it is possible to recover from ransomware, and Panda Dome can keep you and your devices protected in the future.






