Even though passwords keep everything from our bank accounts and medical records to social media and online shopping accounts safe, 66% of Americans still use the same password across their platforms.
If a hacker can crack one of your accounts, it’s possible that most — if not all — of your sensitive data could be compromised. To protect yourself from this, it’s important to learn how to make strong passwords that can guard your digital life.
Follow our recommendations and security tips to create passwords worth protecting in a password manager.
10 Tips for Creating a Strong Password
Passwords are a common part of everyday life, and they should be taken seriously. Many sites or organizations will include password rules for users creating an account, but there is more to password creation than these guidelines.
Some common tips and tricks for creating passwords include:
- Use numbers, letters and special characters
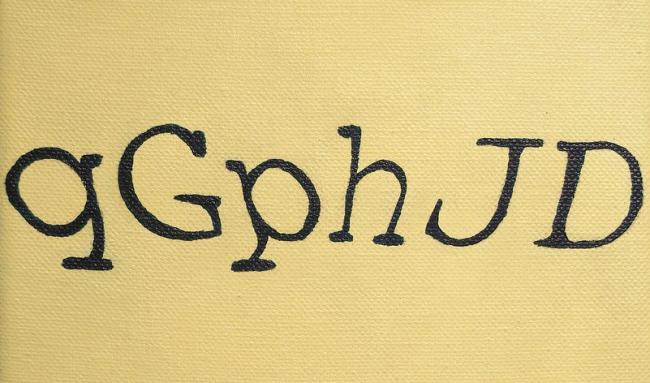
- Combine upper and lower case letters
- Never use a sequence of numbers or letters like 123456, 987654 or abc123
- Never use a sequence of keyboard keys like qwerty or asdfg
Additionally, these following 10 tips dive deeper into the world of password creation to help you build unique, secure passwords for any type of account.
1. Avoid Simple Passwords
It main seem like an obvious tip, but creating complex passwords is an important step in securing your information. Stay away from simple passwords like:
- password
- abc123
- 0000
- aaaa
- 123456789
Any of these passwords could easily be guessed or cracked by a hacker, and many of them fall victim to classic password mistakes. If you’re going to create a password, stay away from simple, ordinary phrases.
2. Don’t Recycle Passwords
Don’t reuse passwords you’ve used in the past, even if you haven’t used them in years. This is especially important if your password has previously been hacked or any of your accounts have been compromised.
3. Utilize a Password Generator
If you’re not comfortable creating a strong password, use a password generator! These security tools are usually free, and they can quickly produce multiple password options. However, these passwords as usually more difficult to remember because their character placements are random.
4. Choose a Passphrase
If you want to make strong passwords, string multiple words together to create a complex passphrase. Because password-cracking software can guess related words, it’s best if the words in your passphrase aren’t obviously connected. You can even increase your passphrase’s strength by including numbers and special characters.
- Bad: password987
- Good: bicycle_shirt-phone!74

5. Use Nonsensical Combinations
Have you ever had a site or account recommend a password that looked something like “LTy56nM3!Uf4rB”? These passwords are frequently suggested because their nonsensical arrangement makes them incredibly difficult to guess. If you’re looking for a strong password, consider storing those with nonsensical combinations in a password manager so you aren’t forced to memorize random letters and digits.
6. Incorporate Codes or Acronyms
Character substitutions, texting acronyms and number codes can all help strengthen your passwords. For example, you can use:
- “3” in place of the letter “E”
- Text acronyms like OMW, TTYL and TMI
- State acronyms like NY, CA and TX
- Personal acronyms for organizations — Amazon could be AZ or Target could be TG
- Digit codes like the number of pages in your favorite book
If you choose to include acronyms or codes, use unique options that aren’t tied to your personal information or a company’s official branding.
7. Consider Length
While shorter passwords may be easier to remember, they are weaker than their longer counterparts. As a good rule of thumb, create passwords that are at least 8 characters long.
8. Don’t Rely on Keyboard Paths
Passwords created using sequential keyboard paths are some of the most easily crackable. While passwords — like QWERTY — may be easy to type and remember, they are created using common, almost universally known keyboard paths.
9. Include Special Characters
Numbers and letters are easily used to create memorable passwords, and including special characters can be an additional way to ensure password security. Not all sites or systems will let you use any symbol you want, but some commonly accepted symbols include:
- Exclamation points (!)
- Dollar signs ($)
- Brackets ([])
- Question marks (?)
- Colons (:)
- Ampersands (&)
10. Account for Brute Force Attacks
Hackers may use brute force attacks to attempt to crack passwords, so creating a brute force-proof password can help protect your information. To do this, your password should:
- Be more than 15 characters long
- Use multiple character types, including upper and lower case letters
- Avoid guessable character substitutions or keyboard paths
- Include nonsensical character arrangements
Common Password Mistakes
When creating different accounts, it can be difficult to come up with unique passwords every time. However, you can still keep your information secure by staying away from these common password mistakes.
- Personal information: Never include personal information like birthdates, names or birthplaces in a password.
- Single dictionary words: Hackers and password programs can quickly guess single dictionary words so make sure to use a passphrase.
- Length: Passwords should be at least 8 characters long but passwords with 15 or more characters are considered the strongest.
- Common words or phrases: If you’re creating a passphrase, stay away from common phrases or connectable words.
- Unmemorable passwords: Unless you’re using a password manager, keep your passwords memorable — otherwise, you’ll have to recover or change your passwords in the future!
- Default passwords: Immediately change the passwords to any accounts that are set up with a default password.
- Identical passwords: If you never vary your passwords, your entire digital world could be accessed by hackers.
If you’re afraid your password may contain a common mistake, there are plenty of free, online password checkers you can use to test a password’s strength.
How to Keep Passwords Safe
Even if you’ve learned how to make strong passwords and you’ve secured your accounts well, it’s important to keep them safe. In order to keep your passwords protected and avoid getting hacked:
- Utilize a password manager. If you create long, nonsensical passwords but can’t memorize them — don’t worry! With a password manager, you’ll only need to memorize your manager’s password.
- Authorize two-factor authentication. Two-factor authentication (2FA) is a standard security practice that requires verification through SMS codes, facial recognition or other measures before granting account access.
- Download a VPN. A VPN provides additional security when you access the internet from public access points, which can help protect your passwords from different types of cyberattacks.
- Use encryption. Encryption codes messages sent across networks, which can help protect information from public network attacks and cyberthieves.
- Change them regularly. Changing your passwords regularly can deny attackers access to your information, even if they cracked your old password.
- Invest in antivirus software. Many hackers will use malware — like ransomware or viruses — to break passwords, so antivirus software can alert you to any malicious or dangerous activity.
Additionally, you can better guard your passwords if you don’t:
- Write them down. Nowhere is safe — including in your mobile device or your address book. You mustn’t have passwords written next to your computer.
- Share them. Even if you trust someone, it’s best to keep your passwords private. If you accidentally slip or need to share them, change your password to something new in the future.
- Store them in your browser. Even though it’s more hassle, it’s better to enter your password manually whenever you visit a site to restrict others from accessing your accounts.
Passwords are usually the only barrier between your information and a hacker, so knowing how to make strong passwords can keep you safe while saving you time and money. If you’re interested in additional password protection, Panda Dome is designed to protect your devices, your privacy and the people most important to you.





9 comments
Definitely great and useful tips Marta. Thanks. I tend to think 8 characters is very weak. I have a password manager called Sticky Password and generate and use passwords with special characters at least 16 characters long and still think it is weak 🙂
Anyway, thanks for the article. Appreciate the information here.
Thanks, Roger. Obviously, 16 characters long is safer than 8, but if you follow all those tips, you’ll get a secure password. Thanks! 🙂
It’s a great tips ,i think that 8 combined characters is safer don’t worry
Good info… I’ve started using four random but common words with spaces between each one.
Sadly, I just don’t trust 8 character passwords anymore.
These are great tips, thanks. I don’t think an 8 letter password is secure enough nowadays either, and symbols are a good way of making a password safer. Password managers are great ideas too, thanks.