After installing Panda Endpoint for macOS manually or remotely, the user is prompted to approve the Panda kernel/system extension on their macOS and the FDA (Full Disk Access) in the case of Catalina 10.15 and higher. |
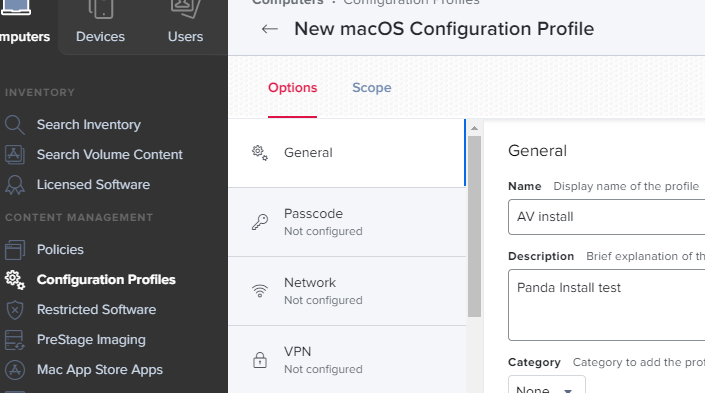
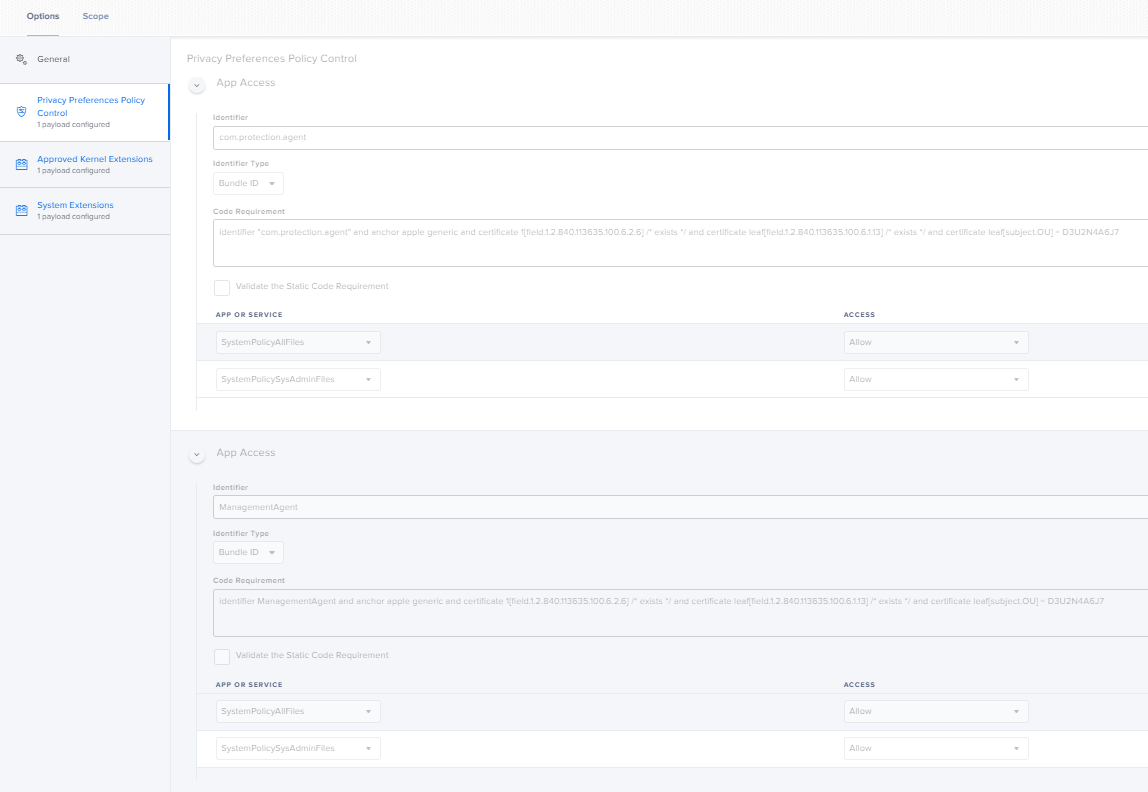
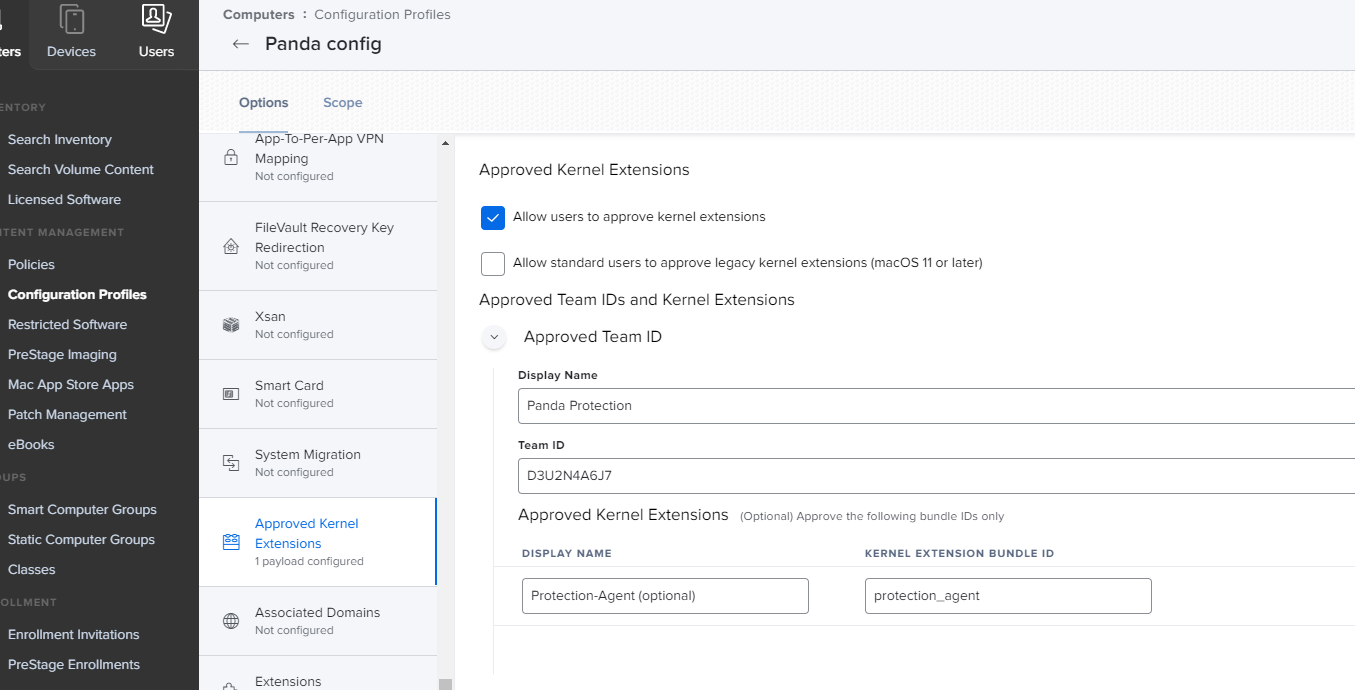
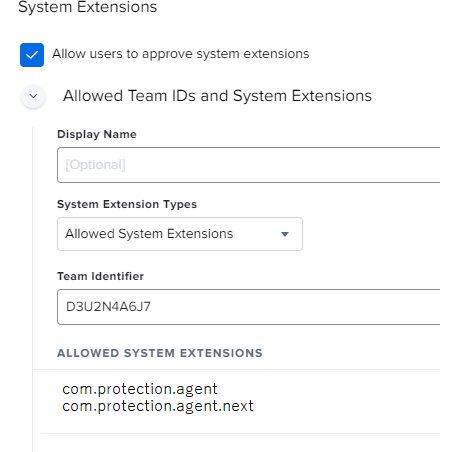
You can pre-approve the Panda kernel/system extension and FDA and thus eliminate user intervention by whitelisting the kernel/system extension using a Mobile Device Management tool such as Jamf Pro. This feature is supported starting with macOS 10.13.2 and Jamf Pro version 10.28.0.
Related Articles |