We are constantly connected in the world we live in today. Picture a typical “connected” day as it is today. We ask “Alexa” the weather forecast in the morning and Google Home to start a timer as we get breakfast started. Then, we head for our morning jog, our every step tracked on a Fitbit. The Internet of Things is everywhere and has become a part of our daily routine.
What is the Internet of Things (IoT)?
We have all heard this term, and to many, it feels a bit ambiguous. IoT or Internet of Things refers to any device that is connected to the internet and is collecting or sharing data. The machine-to-machine (M2M) data that is generated from IoT has an array of uses but it’s most commonly seen as a way to determine the health and status of things.
It includes everything from coffee makers, cellphones, washing machines, wearable devices and headphones. For example, a coffee maker can tell you when coffee is ready, wearable devices determine your health and a washing machine can let your phone know when clothes are complete.
It also applies to components of machines like the jet engine of an airplane. Most likely if a device has an on and off switch to the internet, it can be a part of the IoT. By combining one’s connected devices with automated systems, it’s possible to gather information about the user and learn from a process.

Examples of Internet of Things Devices:
- Wearable devices
- Connected cars
- Intelligent personal assistant
- Smart farming
- Light bulb connected via an app
- Smart thermostat
- Connected toy
How IoT Works
In the Internet of Things, each device has a different purpose. Many are used for collecting data. For example, a wearable device that tracks your daily steps and heart rate helps you monitor your health.
There are three “layers” when it comes to operating IoT devices: the dashboard, cloud and then your devices.
The device sends its signal to the cloud, where other devices are also sending their information to. The cloud is where all the machines interact with each other. From there, this information gets sent to your dashboard, which is where you control your device.

The Internet of Things Ecosystem
The IoT ecosystem refers to all of the components that enable businesses, consumers and the government to connect to their IoT devices. It has been named “the next Industrial Revolution” as it has already begun changing the way people live, work and travel. Business Insider has been tracking the growth of the IoT for more than two years and created an exhaustive report on the IoT ecosystem. We added some of the key results below.
- There will be 34 billion devices connected to the internet by 2020.
- IoT can lower operating costs, increase productivity and expand to new markets for businesses.
- Nearly $6 trillion will be spent on IoT solutions within the next five years.
The History of IoT
The idea of adding intelligence to standard objects has been discussed since the 1980s. In films, “smart devices” were seen as the way of the future. In Back to the Future II, the McFly family uses glasses that serve as a precursor to the Google Glass. The 1990 film Total Recall uses a self-driving car to take Arnold Schwarzenegger around. Smart House, a Disney film from the ‘90s has a completely computerized home.
Humans were curious about Internet of Things, but did not quite have the technology. One early example of IoT is a Coke machine in the early 1980s that allowed programmers to check if Coke was available in the machine before visiting it. In 1990, John Romkey showed that a toaster could be turned on and off by the internet.
The term Internet of Things was first coined by Kevin Ashton during a presentation he made to Proctor and Gamble in 1999. He pushed the importance of radio frequency identification to the company and titled his presentation “Internet of Things.” He emphasized that the internet was one of the hottest trends of the late ‘90s into his talk.
That’s when connected devices began to take off. In 1995, less than 1% of the world’s population had internet access. As of December 2017, more than 54% of the population has internet access. There are 8.5 billion smart devices connected to the internet, with that number increasing substantially each day.

Industries Affected by the Internet of Things
While IoT is expected to help every day consumers stay connected and track their lives, there are several industries that will also benefit from IoT.
These include but are not limited to:
- Agriculture
- Infrastructure
- Manufacturing
- Defense
- Retail
- Banks
- Oil and mining
- Insurance
- Connected homes/smart buildings
- Utilities
- Smart cities
- Healthcare
Major IoT Companies
Hundreds of companies have created devices that link to the Internet of Things and the number will continue to increase in the years to come. Below, we list some of the companies that stand out in the IoT revolution.
- DHL
- Amazon
- Magneto IT Solutions
- Microsoft
- HQSoftware
- IBM
- GE
- Verizon
- Fitbit
- Jasper
- Cisco
- Honeywell
IoT Security and Privacy
IoT is revolutionizing the workplace and how we live on a day-to-day basis. Smart cities are popping up around the world and smart homes give us the capability to ask a question and receive an answer anywhere at any time. While it’s fantastic to stay connected 24/7, it’s important to keep in mind the potential risks and security concerns — like digital amnesia.
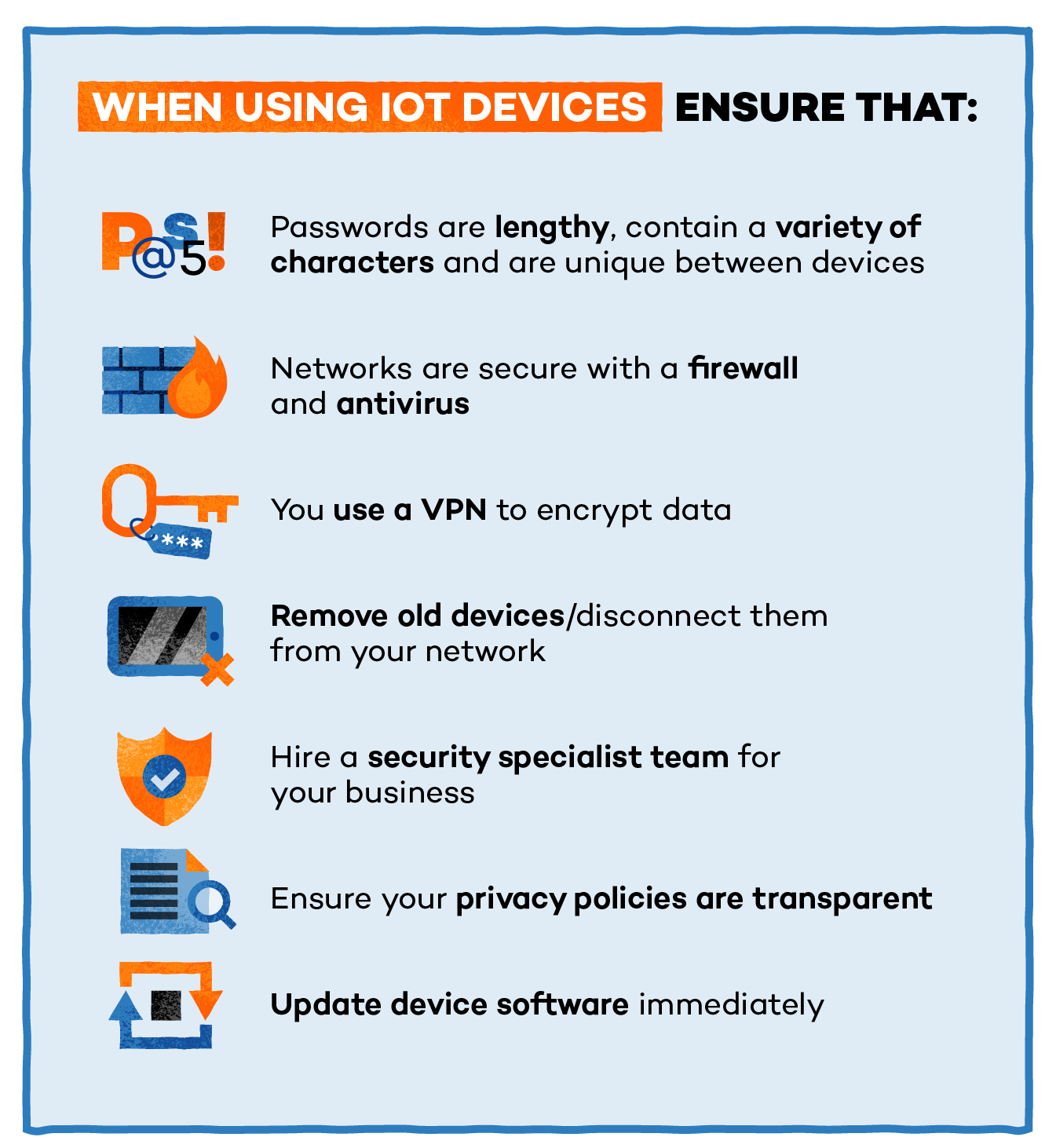
As more connected devices continue to make their way into our daily routines, we are also more vulnerable to hacking. Because the technology is relatively new it’s important to keep in mind that connected devices are not foolproof. Below, we list the top ways to stay secure using Internet of Things devices including using a VPN to encrypt data and remembering to update software regularly.
 The Future of IoT
The Future of IoT
This new world of connected devices allows our environment, including our home and work life, to become smarter and more measurable. Smart speakers make it easy to play music, get quick facts or set a timer. Gamification brings the internet into classrooms with engaging lessons. Home security systems make it easy to monitor your home while you’re away. Smart cars can help us dial numbers and text hands-free, potentially saving thousands of lives. So what’s next for IoT?
A report from Samsung states that the need to secure every connected device by 2020 is critical. Brian Solis from Altimeter Group who worked on future IoT research, states that companies will indulge in digital Darwinism where we learn to rapidly evolve. IoT is also beginning to integrate its data into artificial intelligence systems which take that IoT data and use it to make predictions. For example, Google uses an AI to run its data center cooling system.

Another way IoT is changing the future? Smart city projects are becoming a key feature of IoT. Using data collection sensors over a town or city, planners can get an accurate idea of what’s happening in real time. This could prevent heavy traffic, detect water leakages and locate items in a large warehouse or harbor.
Many cities have begun implementing smart city projects. Barcelona has implemented sensor technology in the irrigation system to detect water quality for plants. Stockholm uses energy-efficient buildings, traffic monitoring and the development of e-services (vs. paper).
Sources:
Business Insider | Think Mobiles | Cloudwares | ZDNet | Forbes | Wired | Business Insider | Internet of Things Agenda | IoT For All |






