Bounty programs became widely used among large technology companies once major firms such as Mozilla or Google had started the trend. Facebook and PayPal were among the companies to follow suit and establish programs that rewarded users – usually computer experts – who discovered security holes in their products. Other companies acknowledge the efforts of such users, though they don’t offer a reward.
So what is the rationale? The idea is that the everyday users of websites and applications discover their vulnerabilities. Such is the importance today of identifying these flaws that many companies spend a lot of money showing their gratitude for the services of those who, in theory, for the love of their art, save these companies from major embarrassment.
There are mutual benefits. The company is able to develop patches to fix the problems -thereby avoiding more serious issues in the future that could have serious economic consequences- and those that detect the issues are rewarded financially. Even when there is no money involved, many white hat hackers are seeking fame and recognition in the world of IT security.
However, you have to be pretty good to find holes in these giants’ programs and you can’t have a hidden agenda. In other words, you need to be the perfect ‘ethical hacker’ or security researcher and devote much of your time to the task.
Google, privacy come first
Google set up its program in 2010. Those looking for rewards can try to find security holes in the google.com, youtube.com, blogger.com and orkut.com domains as well as in Google Chrome, the company’s browser. On its security page, Google defines security holes as, above all, those related to the confidentiality and integrity of the data of users of its services.
In any event, under no circumstances can hackers exploit the bugs directly in the official system, or attack company employees or other Google users. This is something common to almost all companies that offer these types of incentives. Tests may only be carried out on their own accounts. If you want to demonstrate a security hole, do it on your own platforms!
They also explain that certain types of discoveries will not be rewarded financially, although any relevant contribution will be recognized publicly, in a list of names of those who have contributed in some way.
And what sort of rewards are we talking about? These can range from US$ 100 for everyday flaws to US$ 20,000 for highly sensitive vulnerabilities. Not too bad, is it? Yet even so, in the case of really critical bugs, the rewards could be even greater.
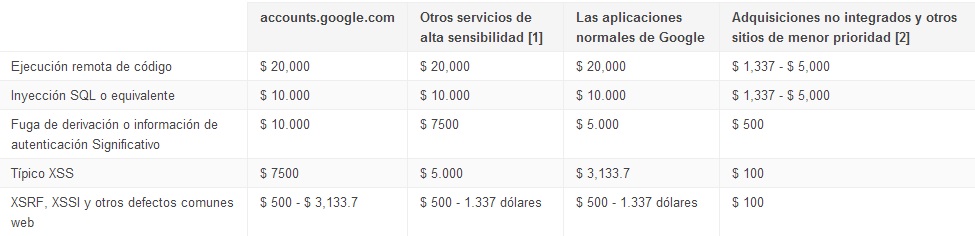
Google Chrome has its own, independent, bounty program, which offers rewards of at least US$ 500, although in practice it has never paid less than US$1,000 and, if the bug is serious, the amount can rise to US$ 3133.70. The official website also states that on several occasions they have paid out US$ 30,000.
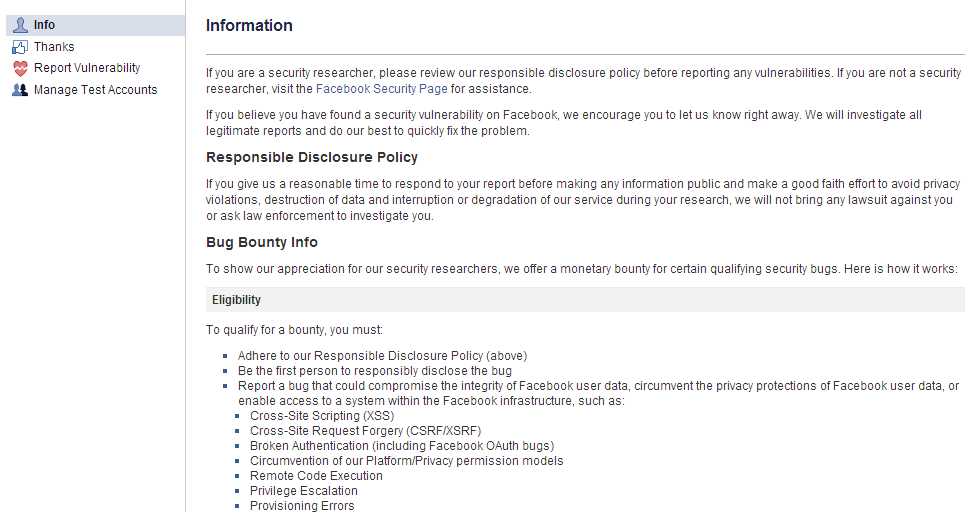
Facebook, on the lookout for security detectives
The leading social network’s bounty program offers a maximum reward of US$ 20,000 and a minimum of US$ 500. However, some researchers have claimed up to US$ 100,000 for detecting major vulnerabilities.
From when the program was launched in 2011 until April 2014, Facebook paid out some US$ 2 million in rewards, and the figure is growing. By August 2013, the company had still only dished out US$ 1 million in rewards to those who had worked to “ensure Facebook stayed safe and secure“. This amount had been shared out among 329 people from 51 different countries. According to the company, two of the researchers who discovered bugs in Facebook now work full-time for the social network. These include Brazilian Reginaldo Silva who earned US$ 33,500 for uncovering an RCE vulnerability that allowed remote execution of code.
To determine the severity of flaws, Facebook has a series of criteria including impact (whether it allows access to private data, if accounts could be deleted or modified); the quality of the explanation (to what extent the person can elaborate on the bug and provide simple instructions on reproducing it); which services are affected (whether it’s Facebook itself, Instagram or any of their smartphone apps); and whether the vulnerability could lead to the discovery of other holes. As a rule, all research is considered valid until proven otherwise.
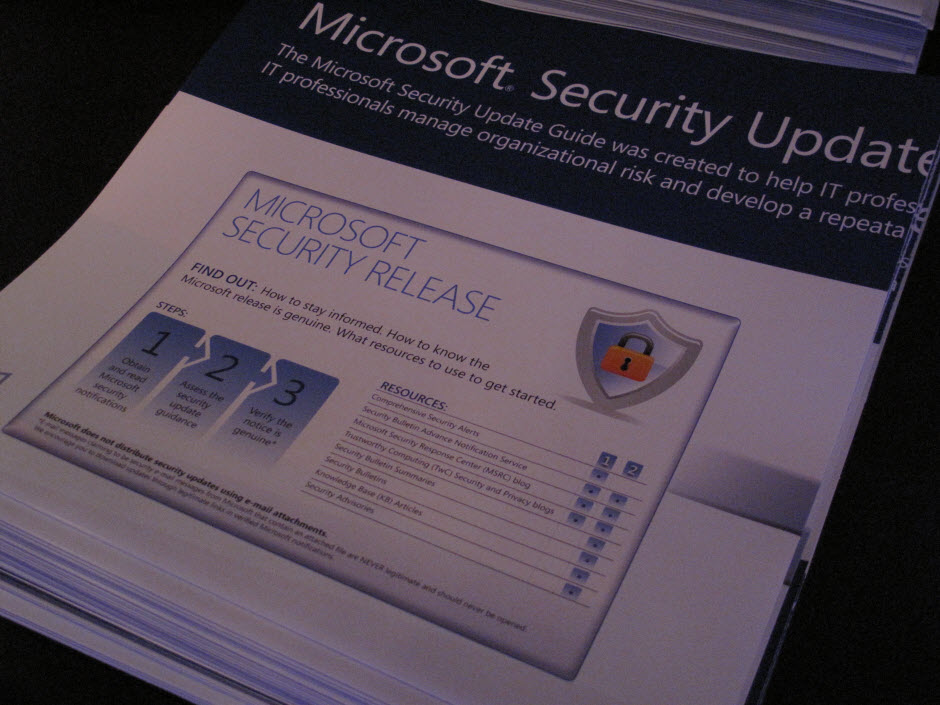
Microsoft, the slowest yet most generous
In June 2013, Microsoft set up three lucrative bounty programs, in fact it’s the most generous company in this respect, despite not previously having acknowledged the efforts of white hat hackers who uncovered bugs in its software. This represented a radical change for the company.
The Mitigation Bypass program offers up to US$ 100,000 to those who find major vulnerabilities on the latest version of the company’s operating system. The BlueHat Bonus for Defense program on the other hand pays up to US$ 50,000 for those who provide ideas for resolving flaws in the program. In total, there’s as much as US$150.000 on offer if you can find and fix an important bug.
The third bounty program, dedicated to Internet Explorer 11, set aside US$ 11,000 for finding bugs in the latest version of the browser. However, the program has been closed as the initial aim was to discover errors in the trial version, before the software was released.
Just a few months after the company had decided to set up a bounty program, British security researcher James Forshaw pocketed US$ 100,000 for his work on Windows 8.1. This was great news for his company, which took most of the profit!
Mozilla, the first and most modest
The Mozilla Foundation may not be as generous, but it does what it can. The rewards it offers to those who detect serious errors are US$ 500, or US$ 3000 in the case of critical vulnerabilities. Not to mention that they also give you a t-shirt with the brand logo! They themselves recognize, on their official website, that their funds are limited, so they ask those who want to participate in their bounty program not to do so if they were working with Mozilla on another project when the flaw was detected.
Albeit not the most generous, this foundation pioneered this type of reward when it launched its program in 2004. There are those who say that this is why Firefox is more secure than Internet Explorer (at least until Microsoft jumped on the bandwagon). Chris Hofmann, director of engineering at Mozilla in 2005, was in no doubt that the bounty program was one of the best ways to “achieve secure, protected software.”
From when the program started until 2013, Mozilla had paid out a total of US$ 570,000 in rewards.
The meanest
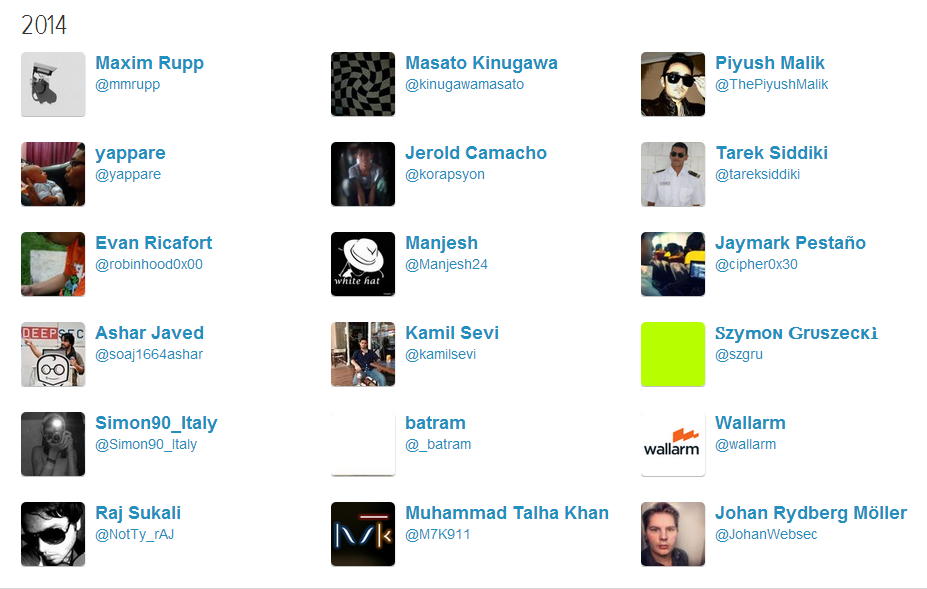
Not all the leading technology firms offer financial rewards to researchers. Twitter and Apple are good examples of this. On its web page, Twitter justifies this with the argument that maintaining the highest levels of security online has always been a joint effort from the community and that they are lucky to have an energetic group of independent researchers who work voluntarily to help them detect possible issues.
At no point do they mention money -probably because there isn’t any-, though they do publish a list of profiles of the users that helped resolve problems in the platform between 2010 and 2014.
The same applies to Apple, who also publish a list on their website of the hackers that have reported vulnerabilities, though they are yet to reach for their pockets.