How to secure the files your company stores in the cloud
Goodbye CD, DVD and pen drive. When you need to share a document with a work colleague or you have to take work home, you…
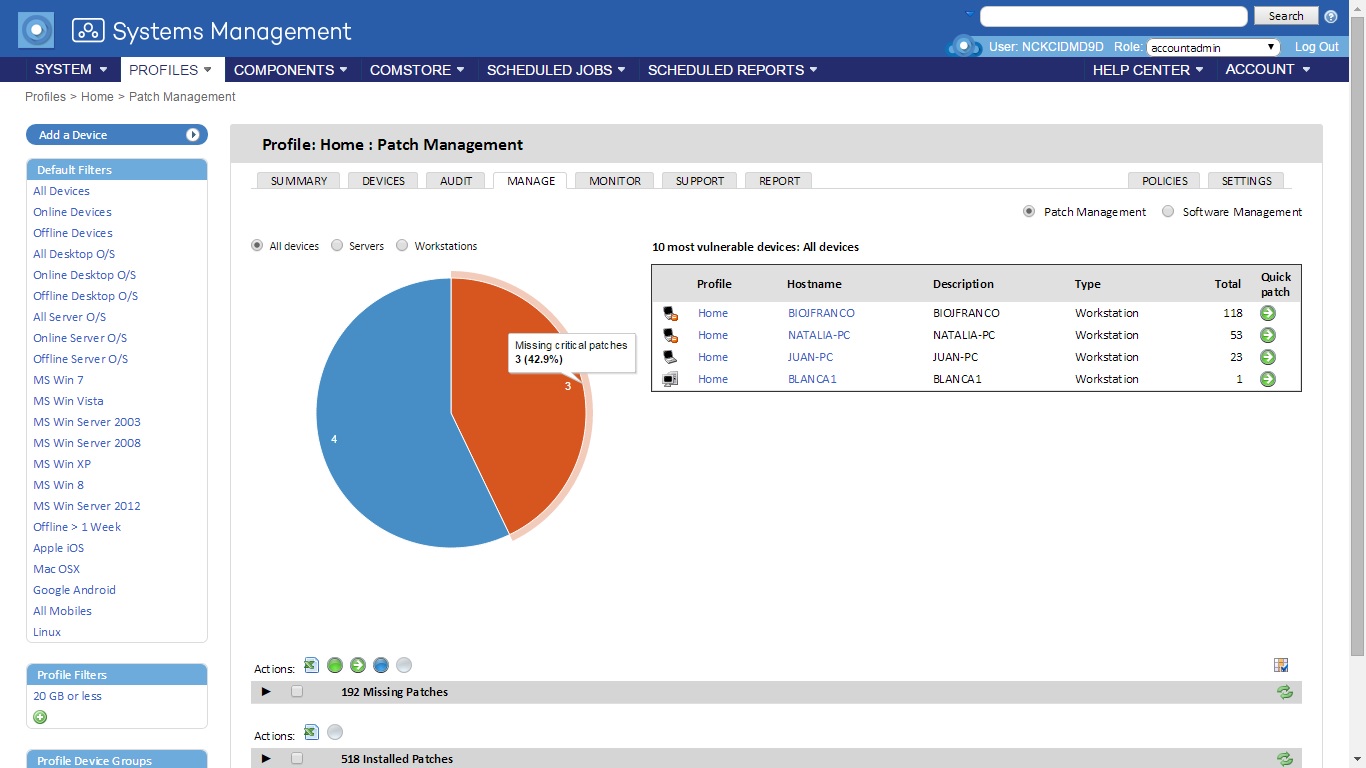
Systems Management strengthens its capabilities to control all types of devices
Panda Security announces the features of the new version of Systems Management, the cross-platform solution that allows you to manage, monitor and provide support to…
Speaking with Gartner about Advanced Persistent Threats
Despite the continuous and growing investments in computer security –Gartner estimated that in 2013 enterprises spent more than $13 billion on firewalls, intrusion prevention systems,…
Dating Apps on your company’s phone. Be careful not to reveal too much personal information!
Your personal life is not incompatible with your professional life, and even less so on your smartphone, a device we use for almost everything these…
The largest bank robbery in history
US newspaper The New York Times has published a fascinating news story about what could be the largest bank robbery in history. According to the…
The vulnerable Internet of Things: Security when everything is connected
The Internet of Things is here to stay. Soon, all of our home appliances will be virtually linked. Televisions, clocks, alarms, cars and even fridges…
10 tips for protecting your privacy when everything seems against it
We are always talking about the dangers that our data often faces in the Internet. Constant leaks and vulnerabilities in the services we use the…