The FBI’s most wanted cyber-criminal used his cat’s name as a password
Not for the first time here, we find ourselves talking about passwords. In January, the software company SplashData listed the most popular passwords of 2013,…
With NFC, even the most expensive smartphones are vulnerable
Nowadays we are defined by our phones. When you buy a smartphone, you automatically become a convert, defending the benefits of your particular brand over…
BlackBerry Messenger. The app that lets you chat only to those you want to.
A few years back, when we discovered that our parents’ business phones could be used for more than just sending emails, something changed. BlackBerry Messenger…
AirHopper, the malware that infects your corporate network even though you are not connected to the Internet
Seems logical, doesn’t it? If your company has ever warned you that you must tread very carefully when browsing the Internet so that your computer…
Panda Internet Security 2015 achieves Virus Bulletin certification
Congratulations are in order! Panda Internet Security 2015 has achieved Virus Bulletin certification! In addition to this good news in itself, we also achieved it…
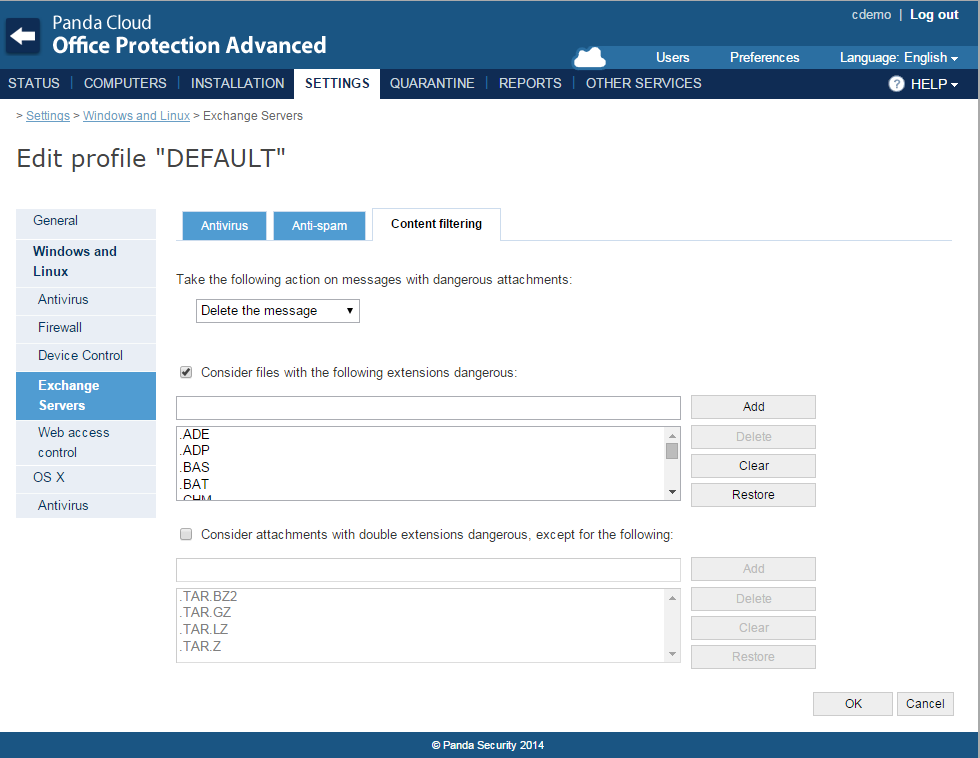
Panda Security launches Panda Cloud Office Protection 7.1
Panda Security, The Cloud Security Company, announces the new features of version 7.1 of Panda Cloud Office Protection (PCOP), Panda Security’s cross-platform solution that offers…
Rootpipe, WireLurker and Masque Attack, the latest vulnerabilities on Apple devices
You have heard it more than once but it is a myth. It always has been. It does not matter how many times you have…